XSS Via XML Value Processing. XXE is not the only vulnerability
Descrição
XXE is not the only vulnerability that can be introduced to a web application when processing XML files. If the values within strings are not handled correctly, it may also be possible for an…

XXE (XML External entity) - secinthemiddle
What Is XXE Processing Vulnerability and How to Fix It?
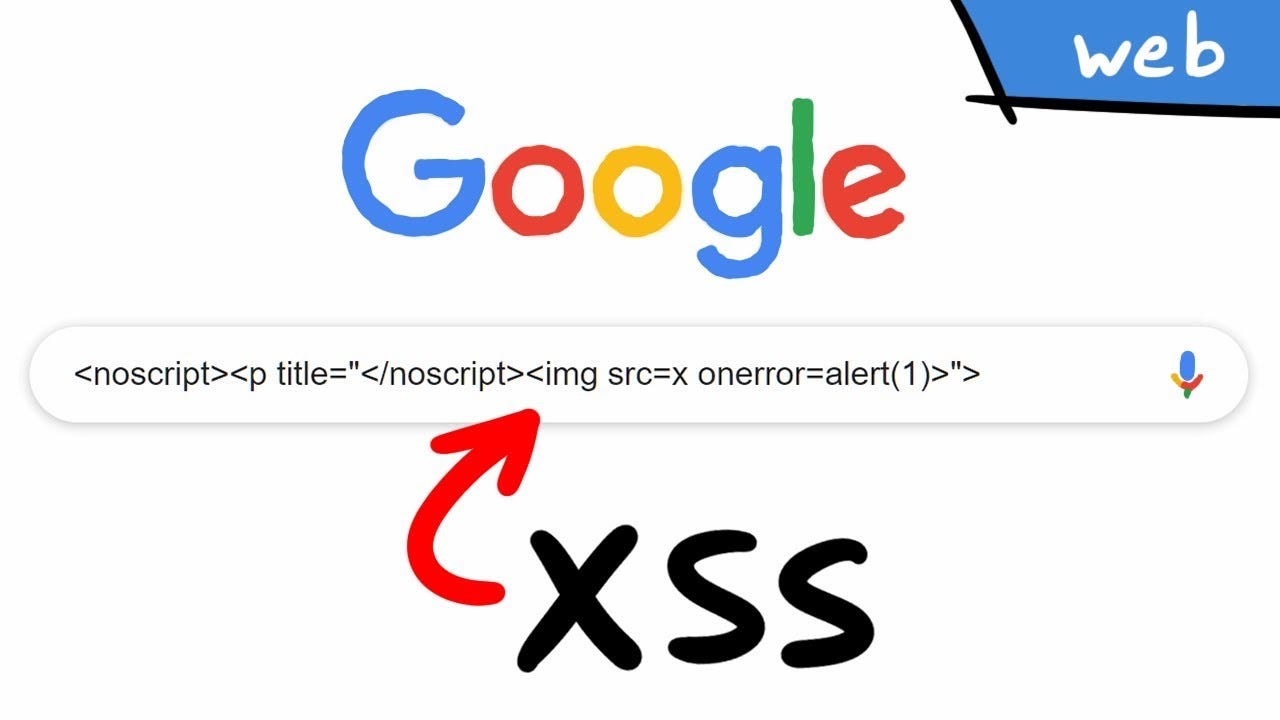
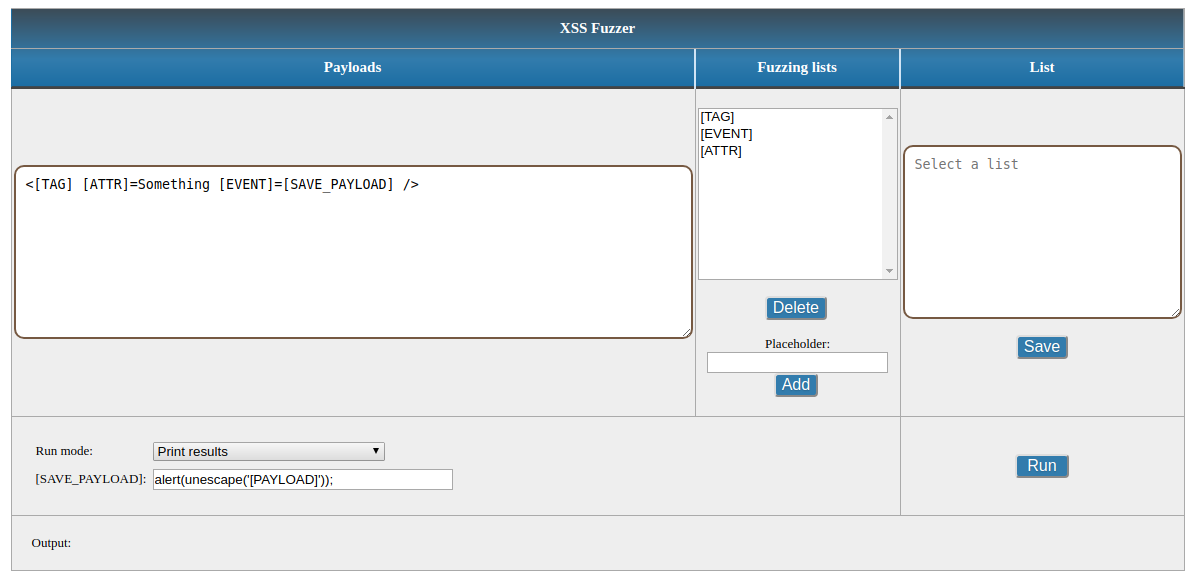
Cross Site Scripting ( XSS ) Vulnerability Payload List, by Ismail Tasdelen

RH-ISAC Top 10 Web Application Security Risks - RH-ISAC

Vulnerabilities due to XML files processing: XXE in C# applications in theory and in practice, by Sergey Vasiliev

Exploitation: XML External Entity (XXE) Injection - Depth Security

Exploitation: XML External Entity (XXE) Injection - Depth Security
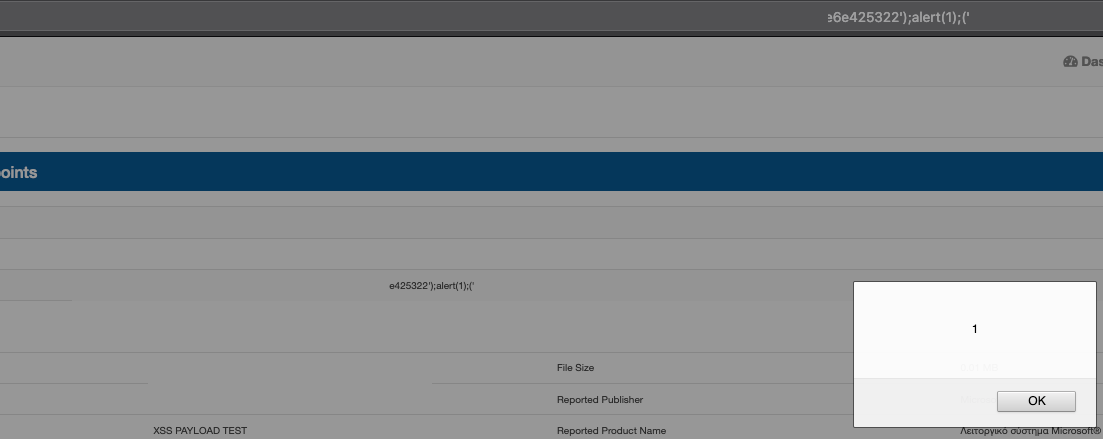
XSS Via XML Value Processing. XXE is not the only vulnerability that…, by Numb Shiva

What is XML External Entity attack (XXE attack) & How to prevent as a developer?
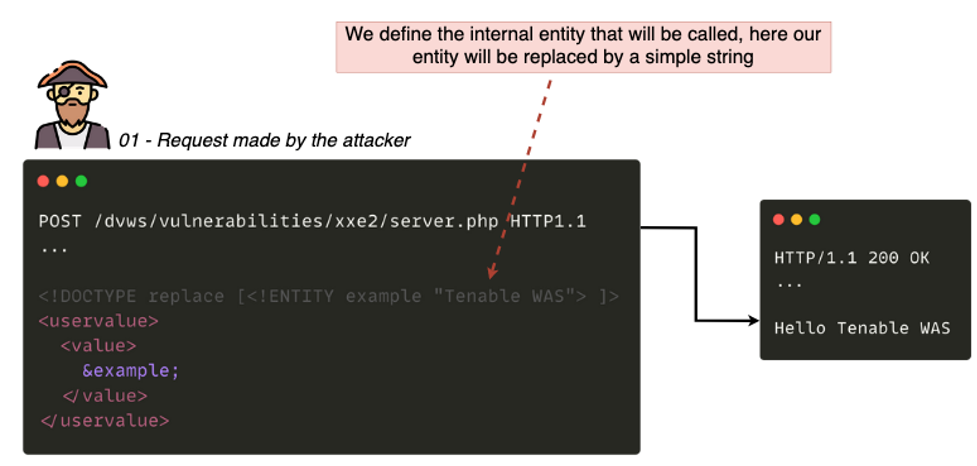
Identifying XML External Entity: How Tenable.io Web Application Scanning Can Help - Blog
XXE Exposed: SQLi, XSS, XXE and XEE against Web Services
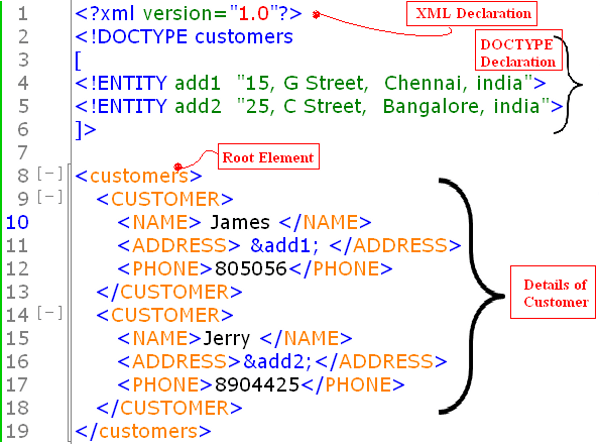
XXE : From Zero to Hero. Hello fellow hackers, I hope you all…, by newrouge
XML injection vulnerability: Examples, cheatsheet and prevention

Vulnerabilities due to XML files processing: XXE in C# applications in theory and in practice
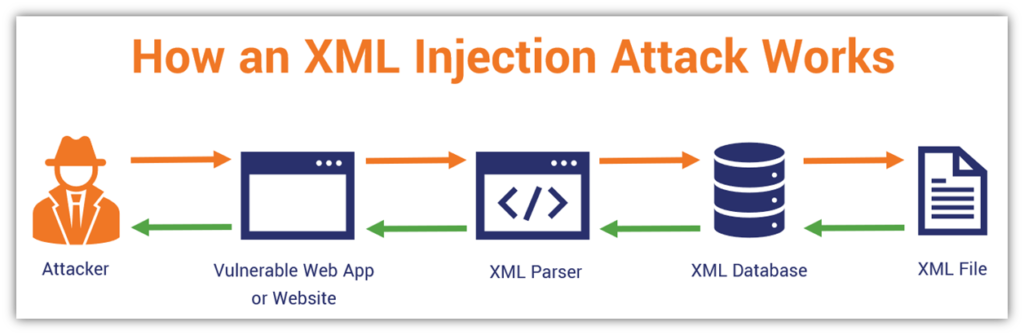
XML Injection Attacks: What to Know About XPath, XQuery, XXE & More - Hashed Out by The SSL Store™
de
por adulto (o preço varia de acordo com o tamanho do grupo)