Attackers use JavaScript URLs, API forms and more to scam users in
Descrição
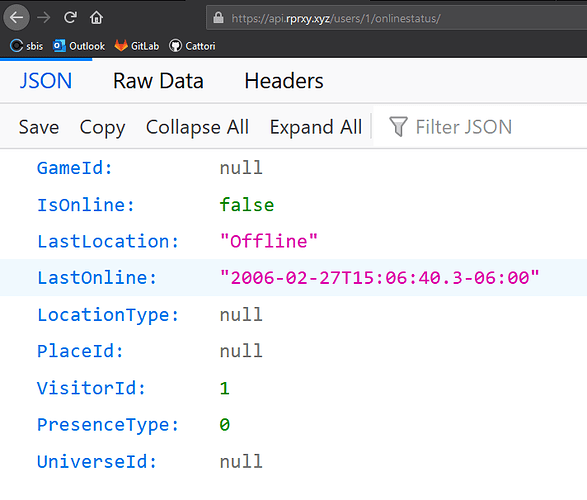
Knowing the common scams is an important step in using the platform safely. The following recommendations help players not fall into scams.
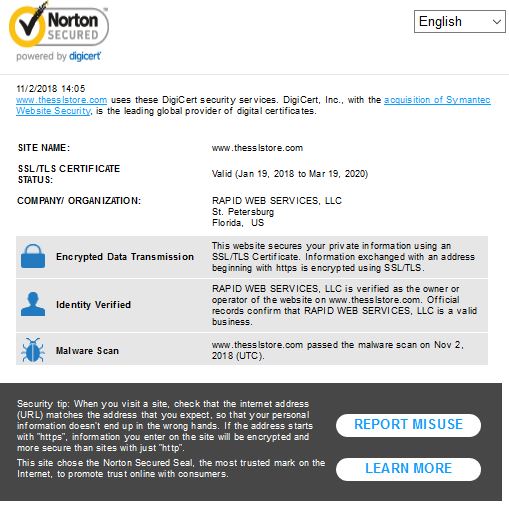
5 Ways to Determine if a Website is Fake, Fraudulent, or a Scam in
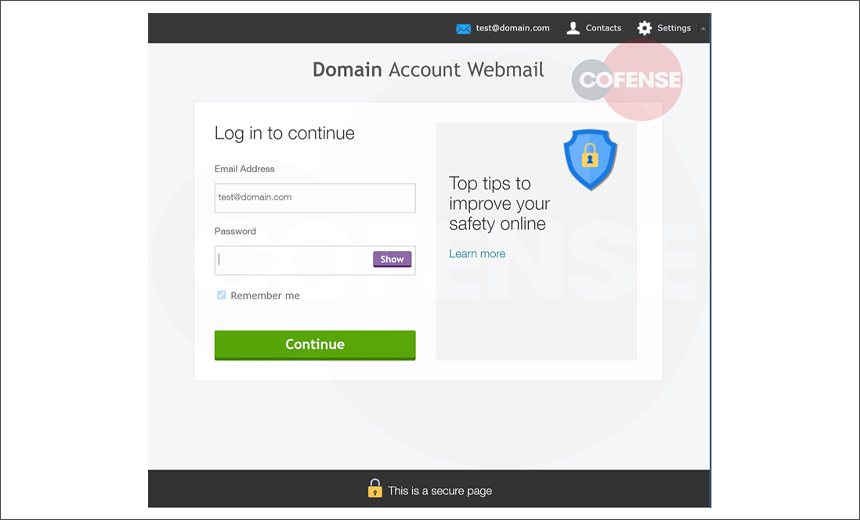
Fraudsters Using Telegram API to Harvest Credentials
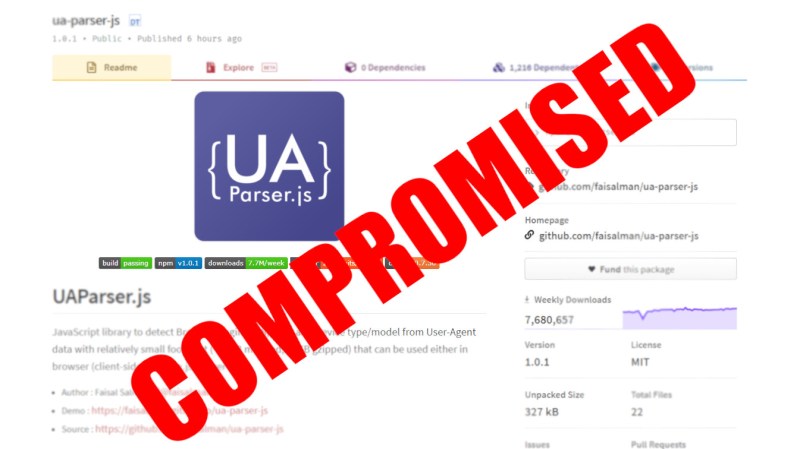
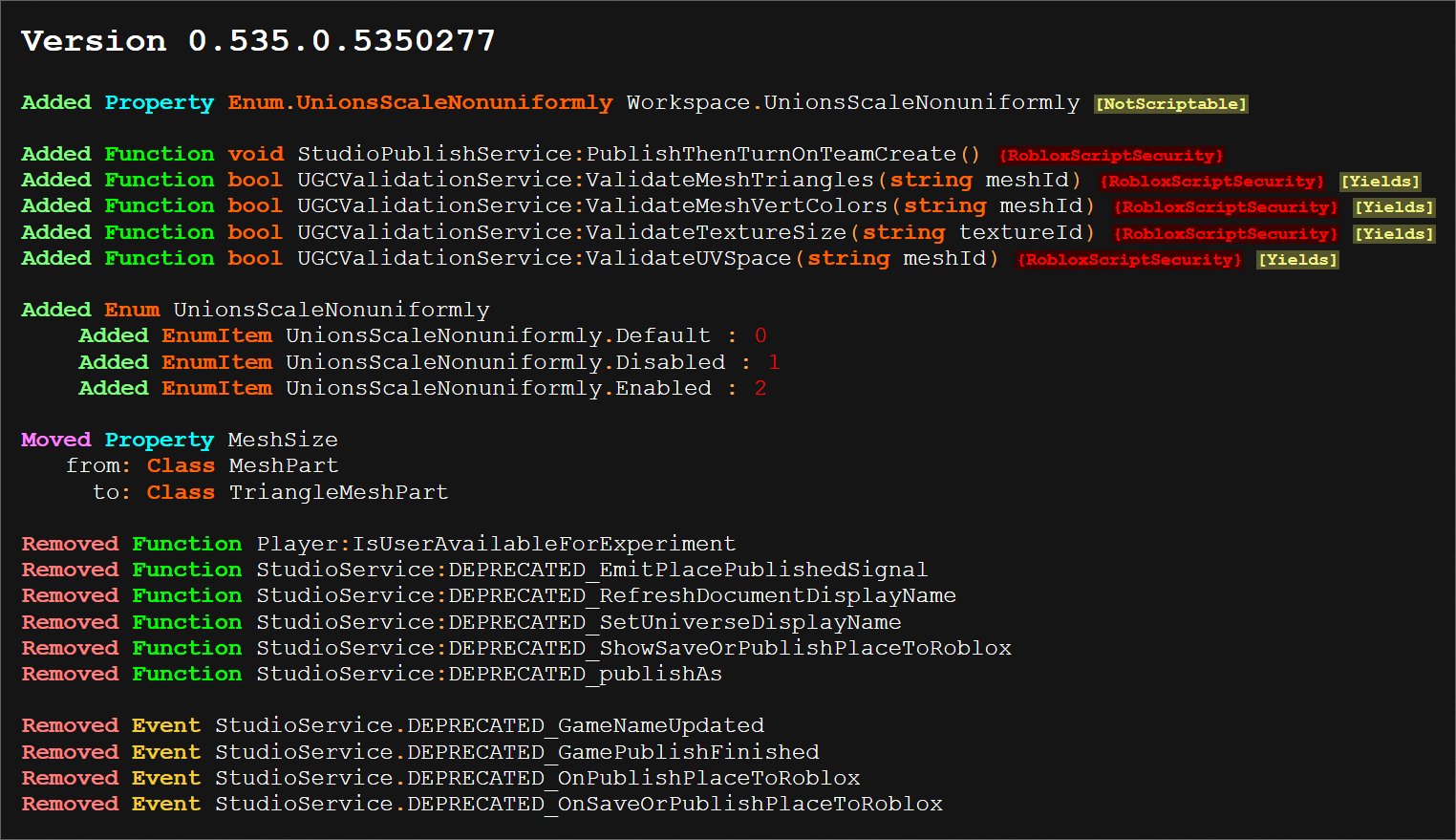
Supply Chain Attack: NPM Library Used By Facebook And Others Was

DONATO VIGGIANO on LinkedIn: Attackers use JavaScript URLs, API
Unvalidated Redirects And Forwards - Ultimate Guide
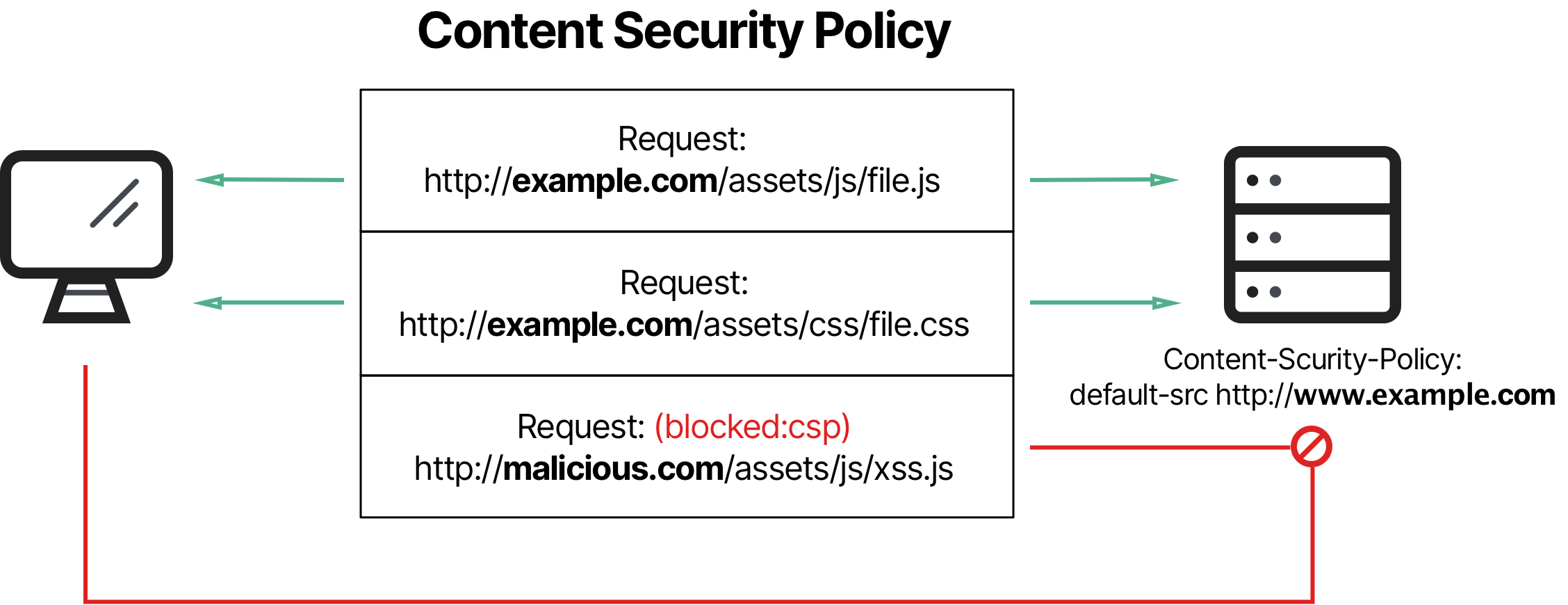
What is Content Security Policy (CSP), Header Examples
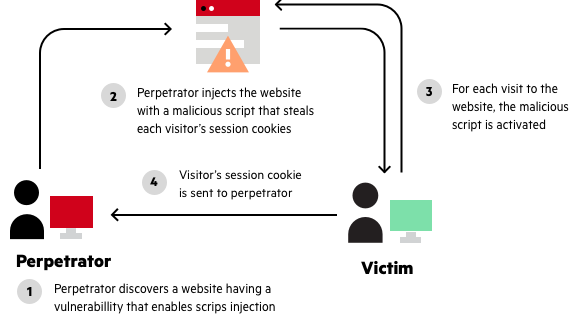
Reflected XSS, How to Prevent a Non-Persistent Attack
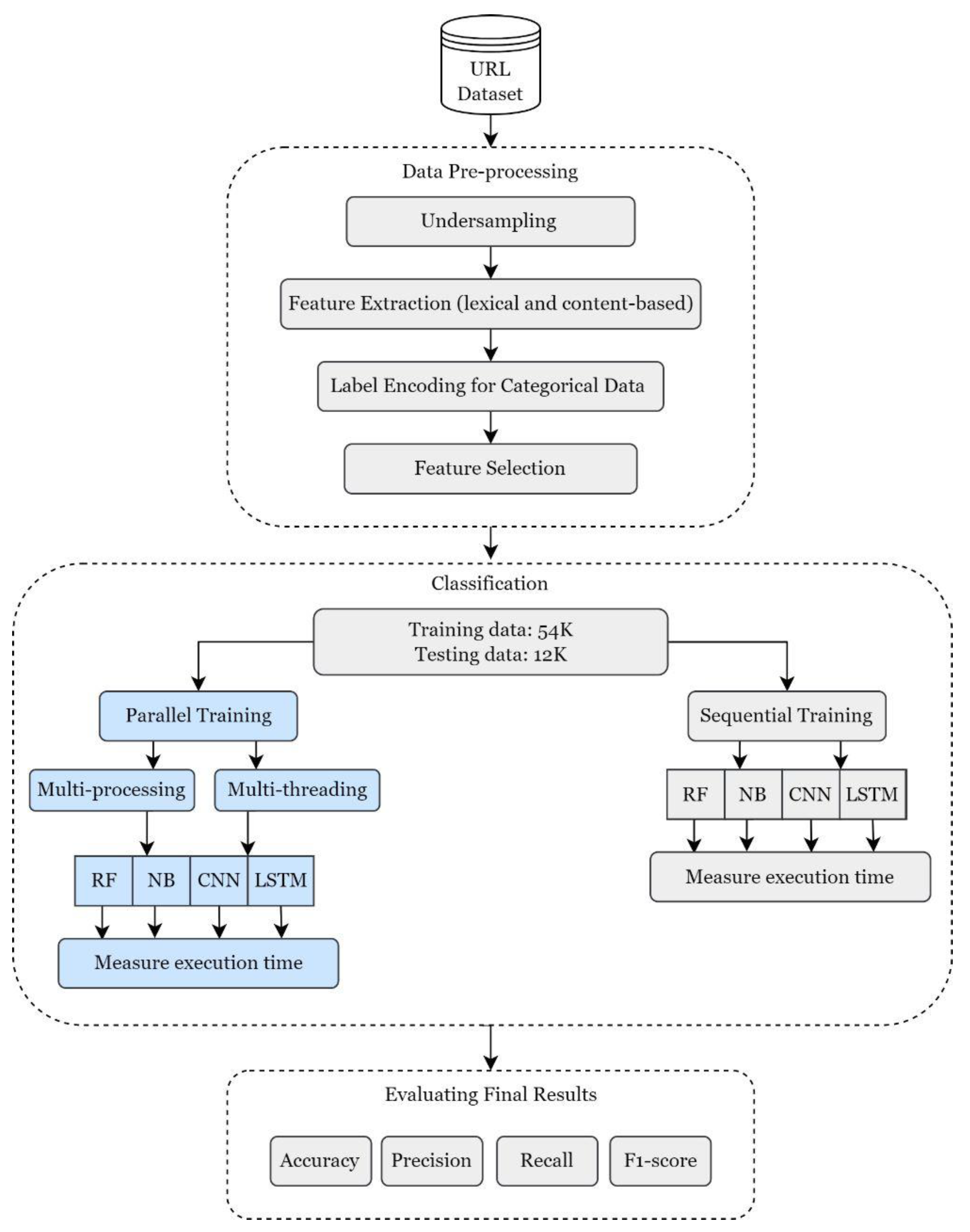
Sensors, Free Full-Text
Defend Your Web Apps from Cross-Site Scripting (XSS)
Cisco on LinkedIn: Cisco Intersight Workload Optimizer Free Trial
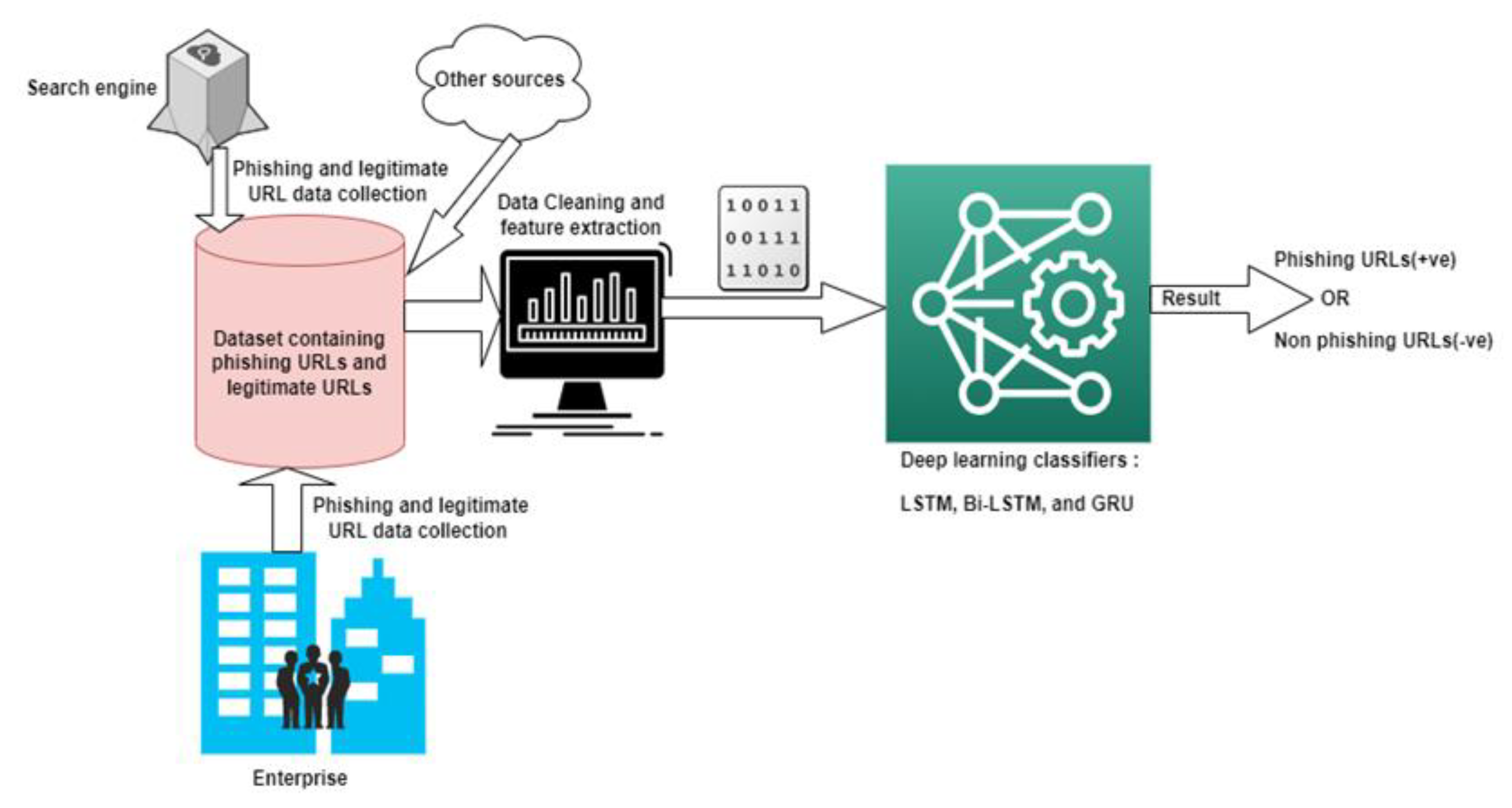
Future Internet, Free Full-Text
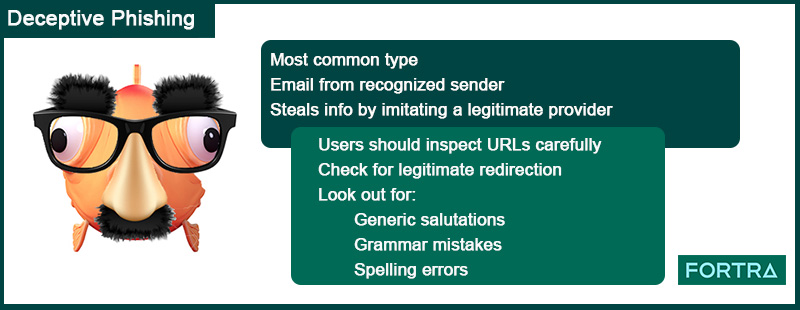
6 Common Phishing Attacks and How to Protect Against Them
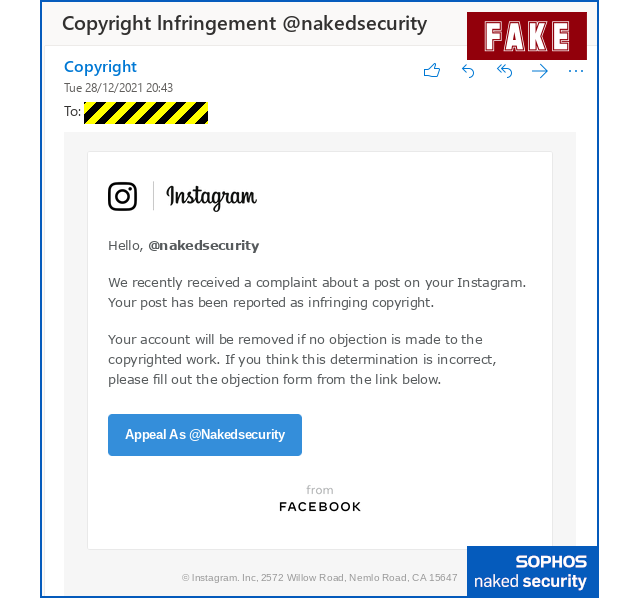
Copyright Infringement Instagram Scam - CyberHoot

Threat Actors Rapidly Adopt Web3 IPFS Technology
Attackers use JavaScript URLs, API forms and more to scam users in
de
por adulto (o preço varia de acordo com o tamanho do grupo)