Malware analysis Suspicious activity
Descrição

What is Malware Analysis
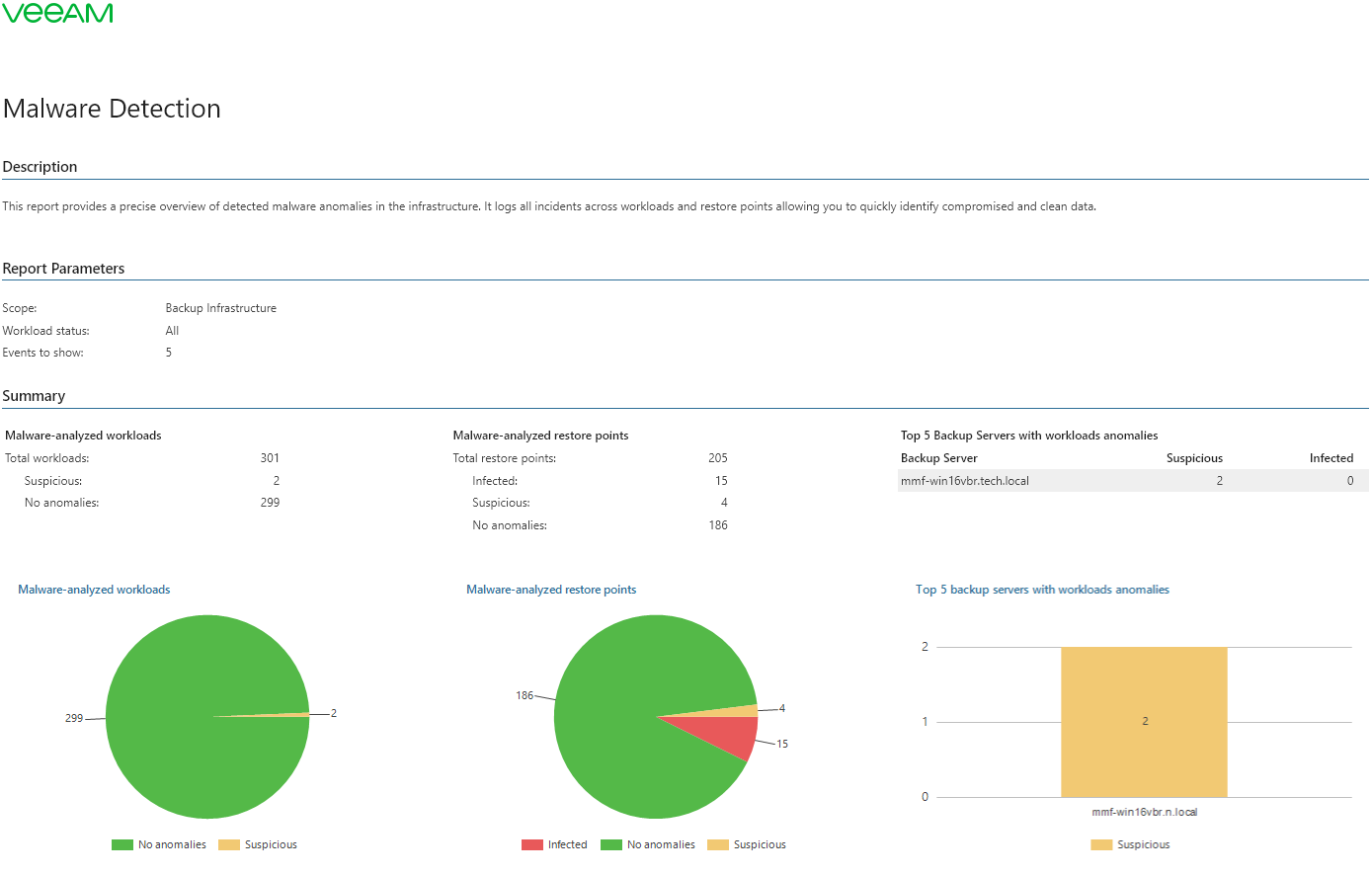
Malware Detection - Veeam ONE Reporting Guide

Malware Analysis and Reverse Engineering, by Ensar Seker
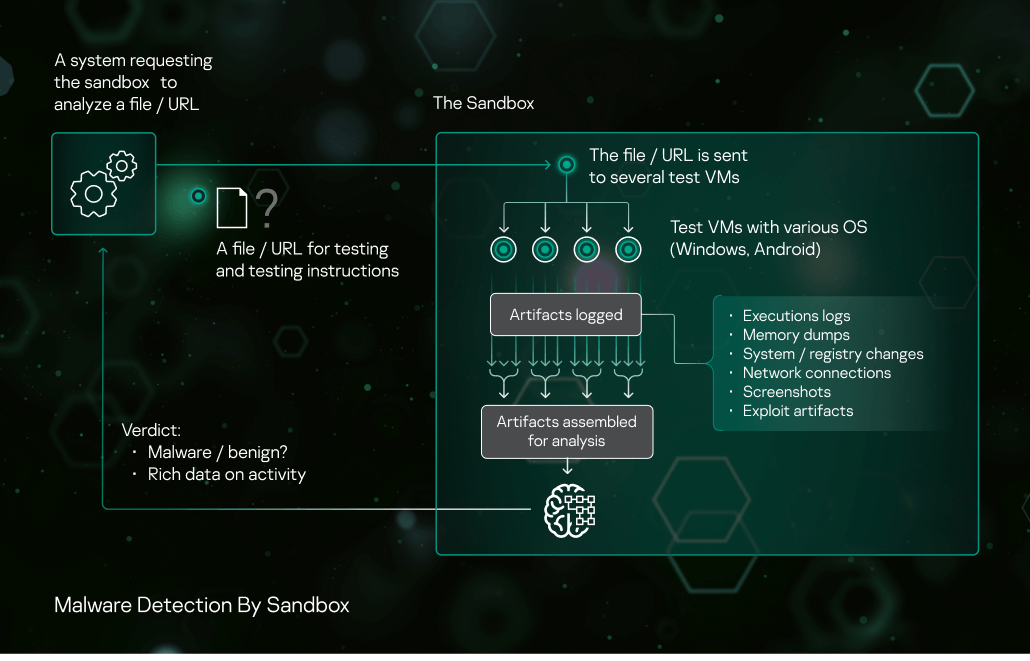
Sandbox Kaspersky

Why Do You Need a Malware Sandbox? - Cyber Defense Magazine

Malware Analysis Use Cases with ANY.RUN Sandbox - Security
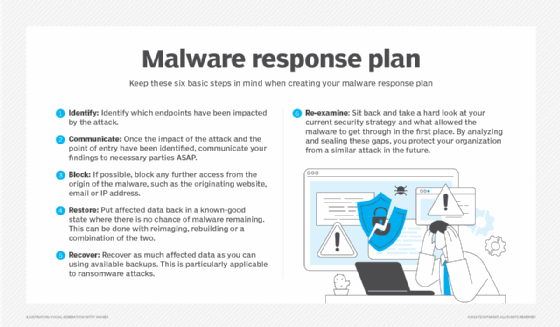
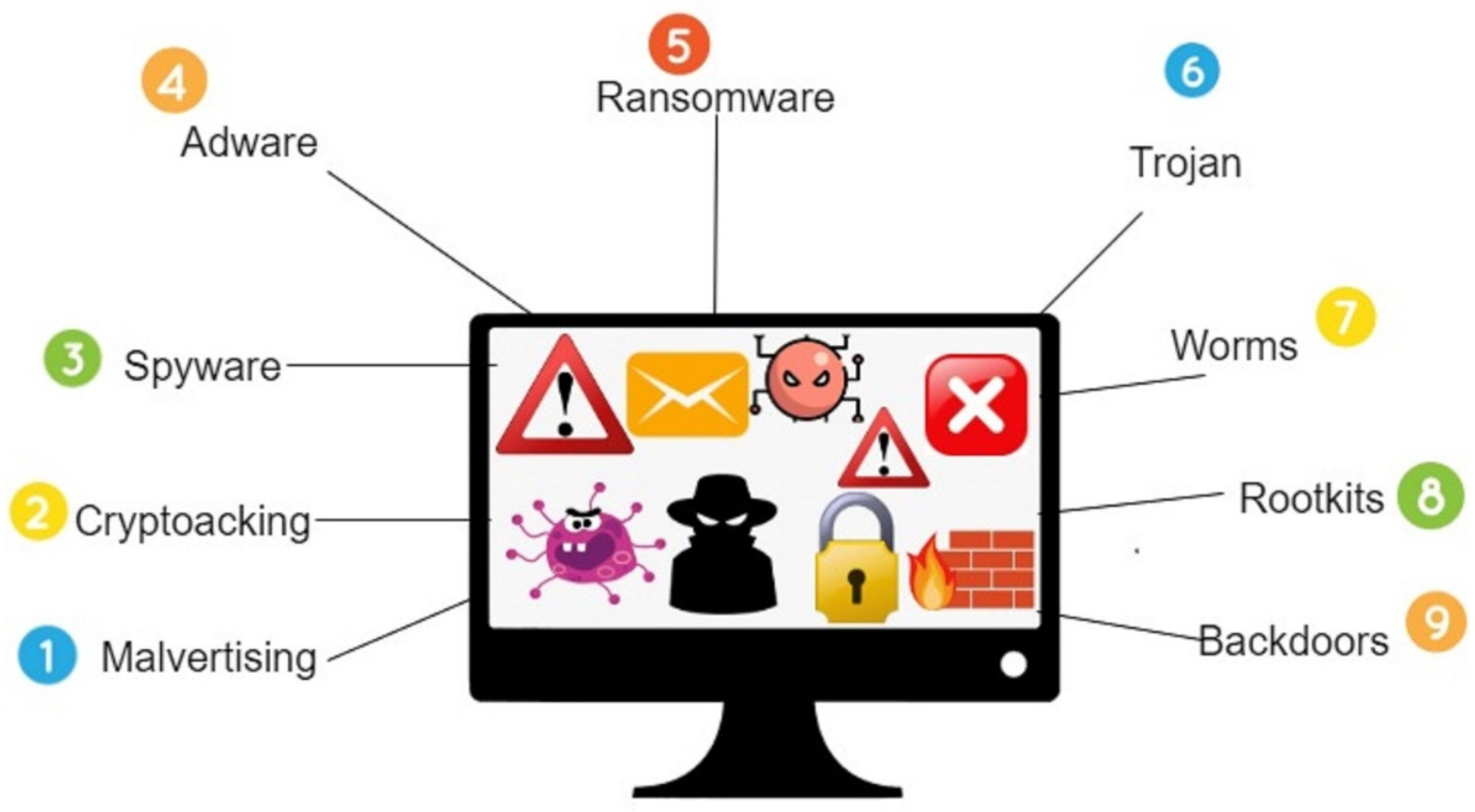
What is Malware? Definition, Types, Prevention - TechTarget

Advanced Malware Detection – Signatures vs. Behavior Analysis

Remove McAfee Suspicious Activity Pop-ups [Virus Removal]
Symmetry, Free Full-Text
de
por adulto (o preço varia de acordo com o tamanho do grupo)