Malware analysis Suspicious activity
Descrição
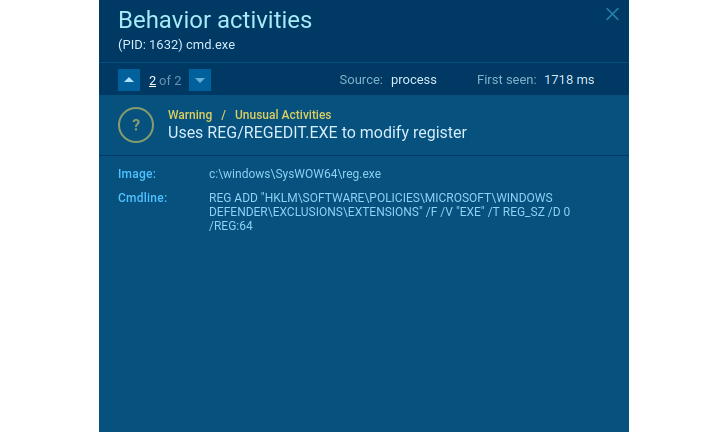
How to Detect New Threats via Suspicious Activities

Security Orchestration Use Case: Automating Malware Analysis
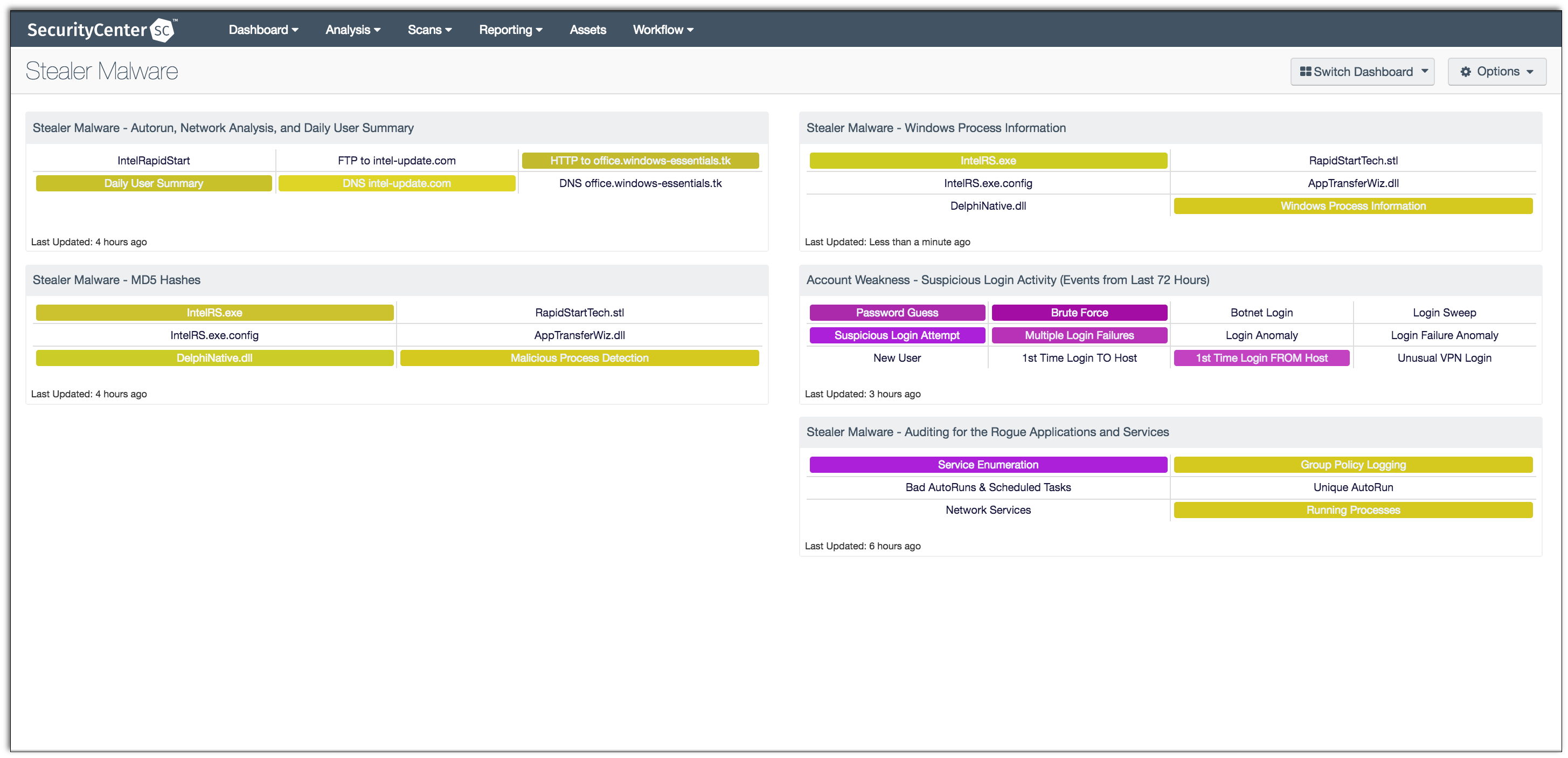
Stealer Malware - SC Dashboard
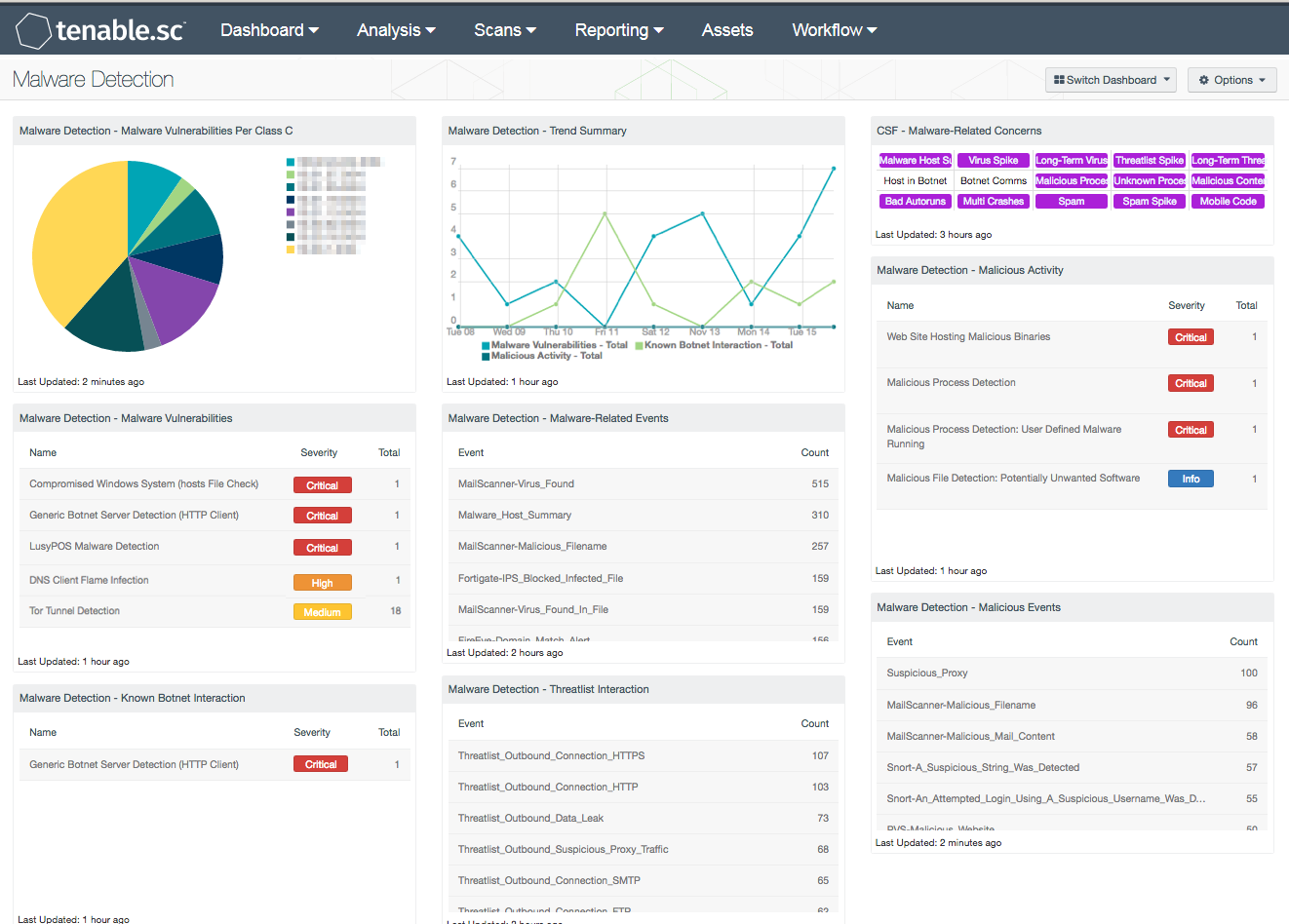
Malware Detection - SC Dashboard

Malware Analysis: Steps & Examples - CrowdStrike
Malware Detection: 7 Methods and Security Solutions that Use Them

Top 10 Malware Analysis Platforms & Tools

Malware Analysis and Reverse Engineering, by Ensar Seker

Malware Analysis - What is, Benefits & Types (Easily Explained)
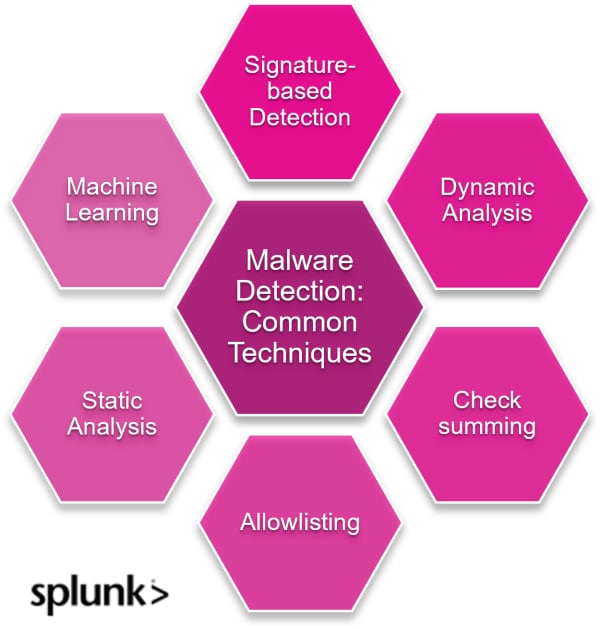
Malware Detection & Top Techniques Today

A flow chart of malware detection approaches and features

The Top 20 Malware Analysis Tools for 2024
de
por adulto (o preço varia de acordo com o tamanho do grupo)