Malware analysis Malicious activity
Descrição

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

MetaDefender Cloud Advanced threat prevention and detection

Malware Analysis: Steps & Examples - CrowdStrike
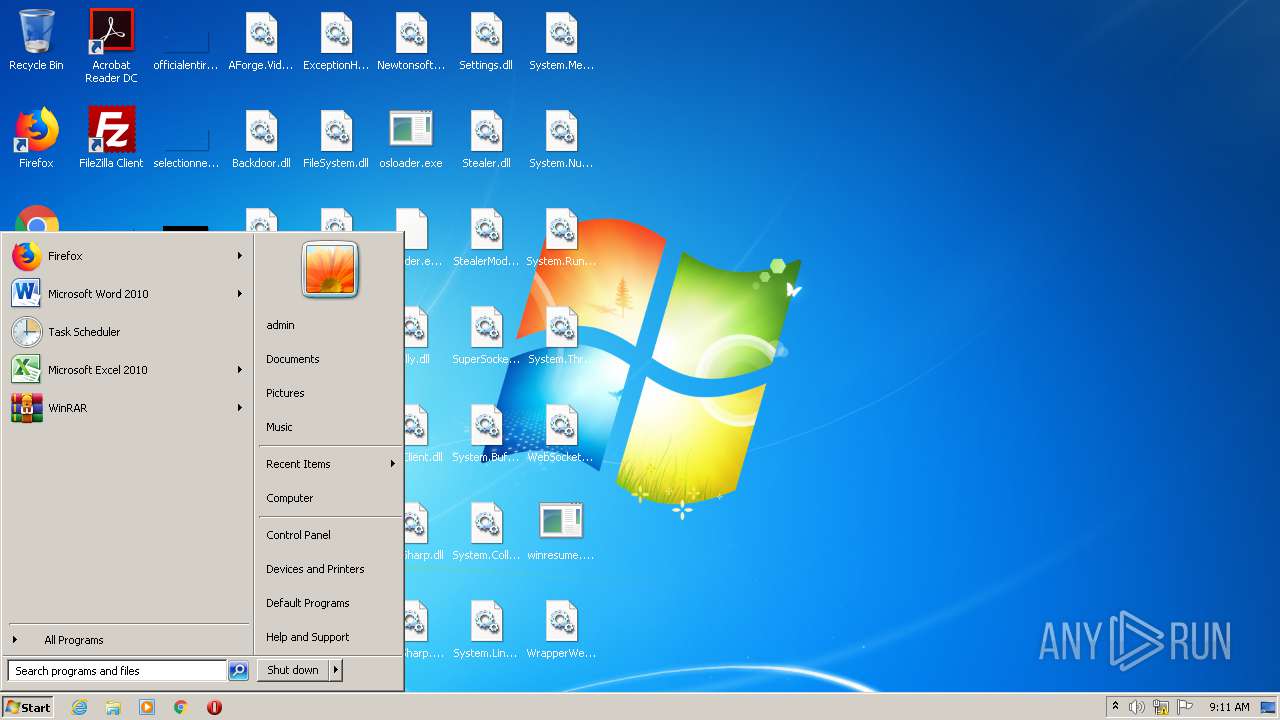
Malware analysis Release.zip Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

What is Malware? Definition, Types, Prevention - TechTarget

Mastering Malware Analysis
Malware analysis index.html Malicious activity

Endpoint Detection and Response, Free - What is EDR Security?

Malware analysis tt.7z Malicious activity

Malware analysis Program_Install_and_Uninstall Malicious activity

Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog

Malware analysis mykey_.rar Malicious activity
de
por adulto (o preço varia de acordo com o tamanho do grupo)