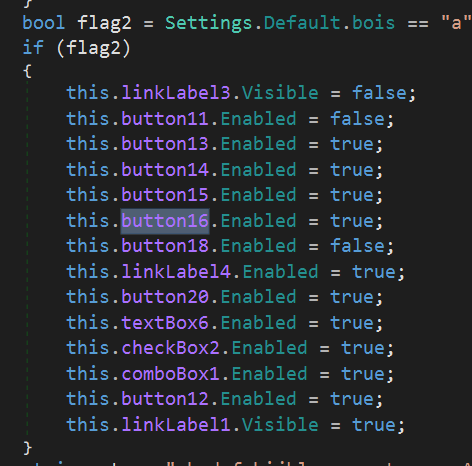
Malware analysis Malicious activity
Descrição

Malware Analysis: Steps & Examples - CrowdStrike

Malware analysis Program_Install_and_Uninstall Malicious activity

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable
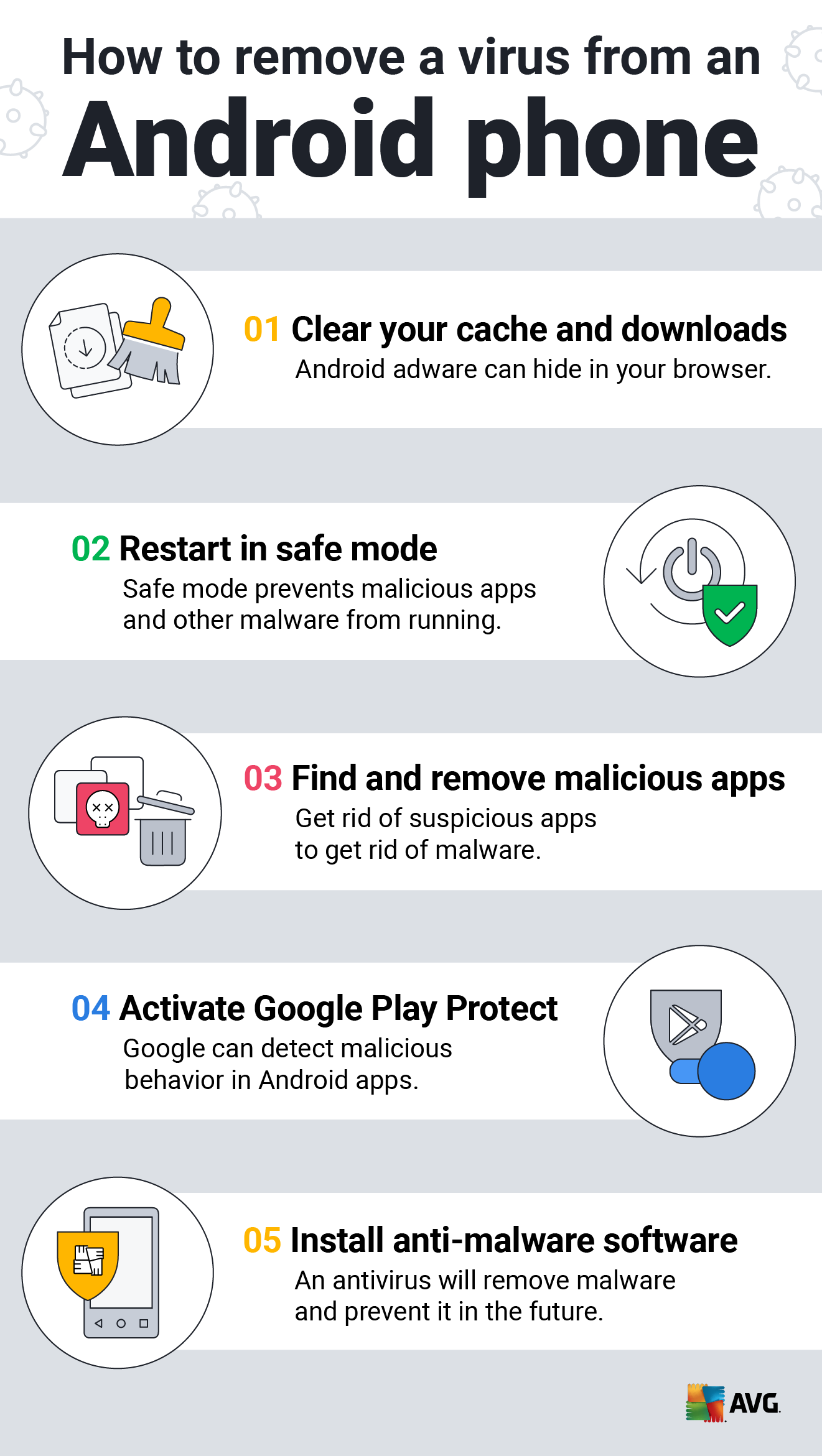
How to Clean an Android or iPhone from Viruses for Free

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber
Malicious URL Scanner, Scan URLs for Malware
Interactive Online Malware Sandbox
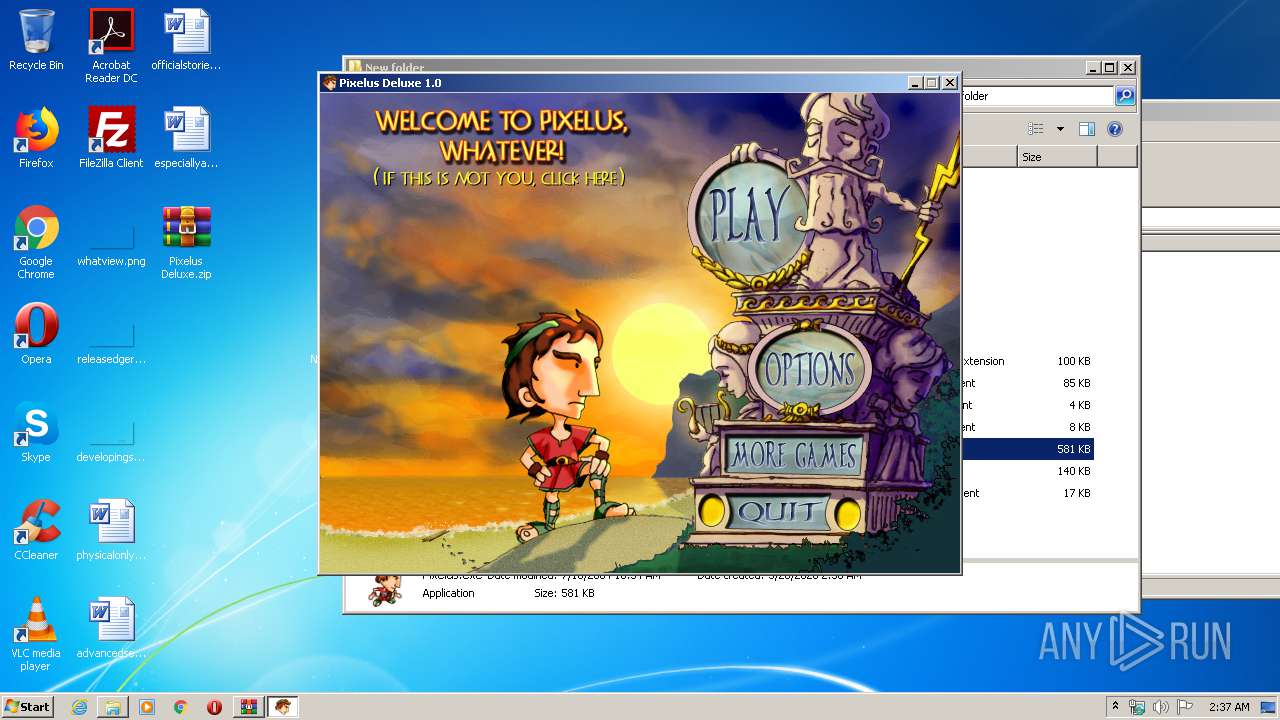
Malware analysis Pixelus Deluxe.zip Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike
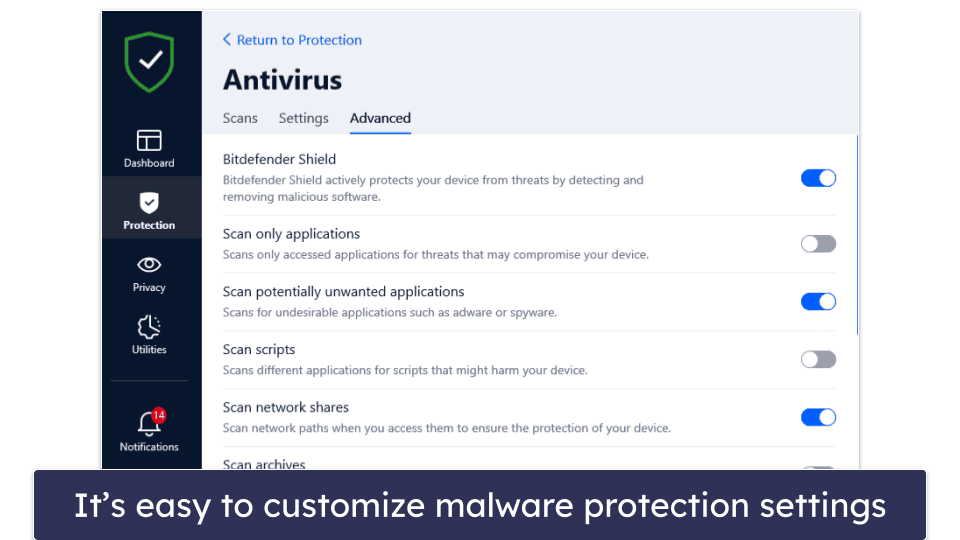
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources

Detail procedure of malware analysis

Malware Analysis: Protecting Your Network from Cyber Attacks
de
por adulto (o preço varia de acordo com o tamanho do grupo)