Malware analysis Malicious activity
Descrição
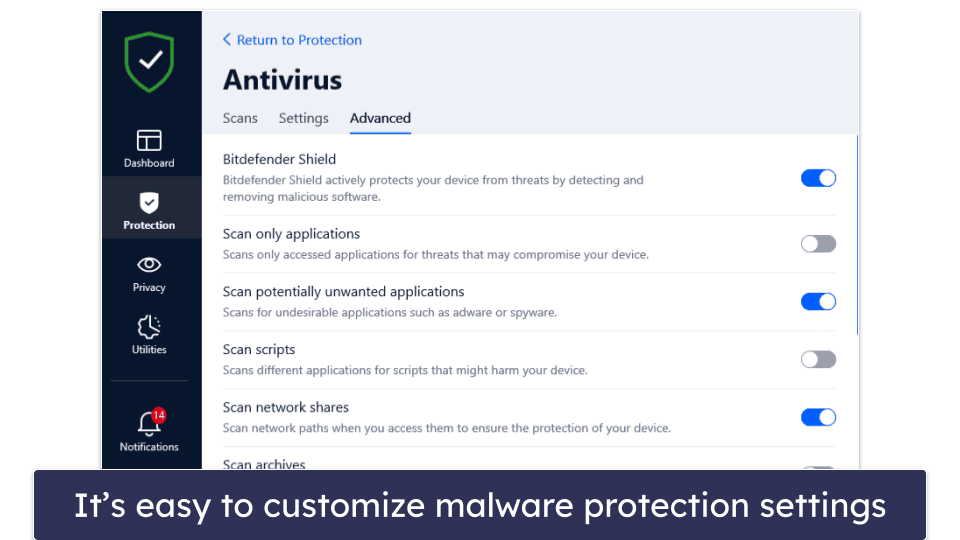
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis: Steps & Examples - CrowdStrike

Security Orchestration Use Case: Automating Malware Analysis

What is Malware? Definition, Types, Prevention - TechTarget
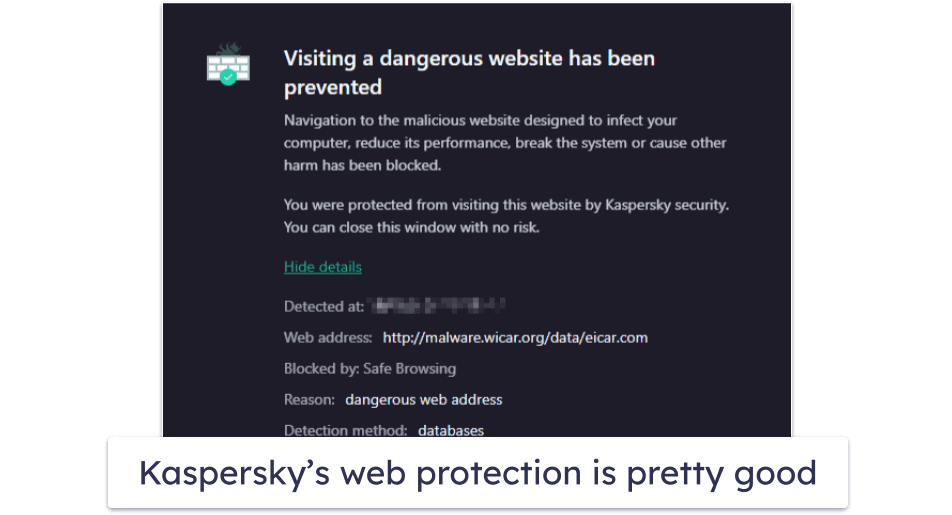
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac

Malware analysis index.html Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Routers Roasting on an Open Firewall: the KV-botnet Investigation

Malware analysis index.html Malicious activity

Comprehensive Protection Strategies Against Cyber Threats
de
por adulto (o preço varia de acordo com o tamanho do grupo)