Malware analysis Malicious activity
Descrição

AlienVault - Open Threat Exchange

Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

Advanced Automated Malware Analysis – Kaspersky Research Sandbox

MetaDefender Cloud Advanced threat prevention and detection

Malware analysis index.html Malicious activity
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources

Robust Malware Detection Models: Learning From Adversarial Attacks and Defenses - Forensic Focus

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable
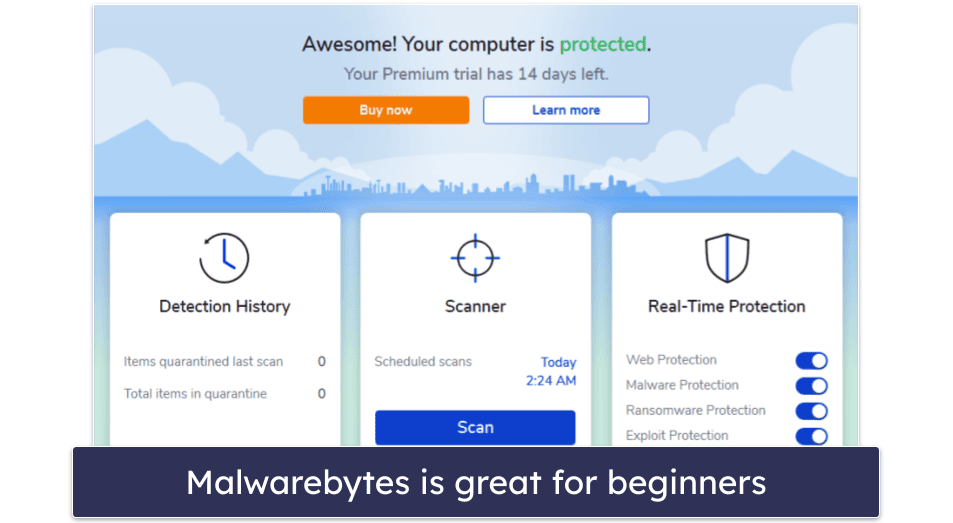
10 Best Antivirus Software in 2023: Windows, Android, iOS, Mac
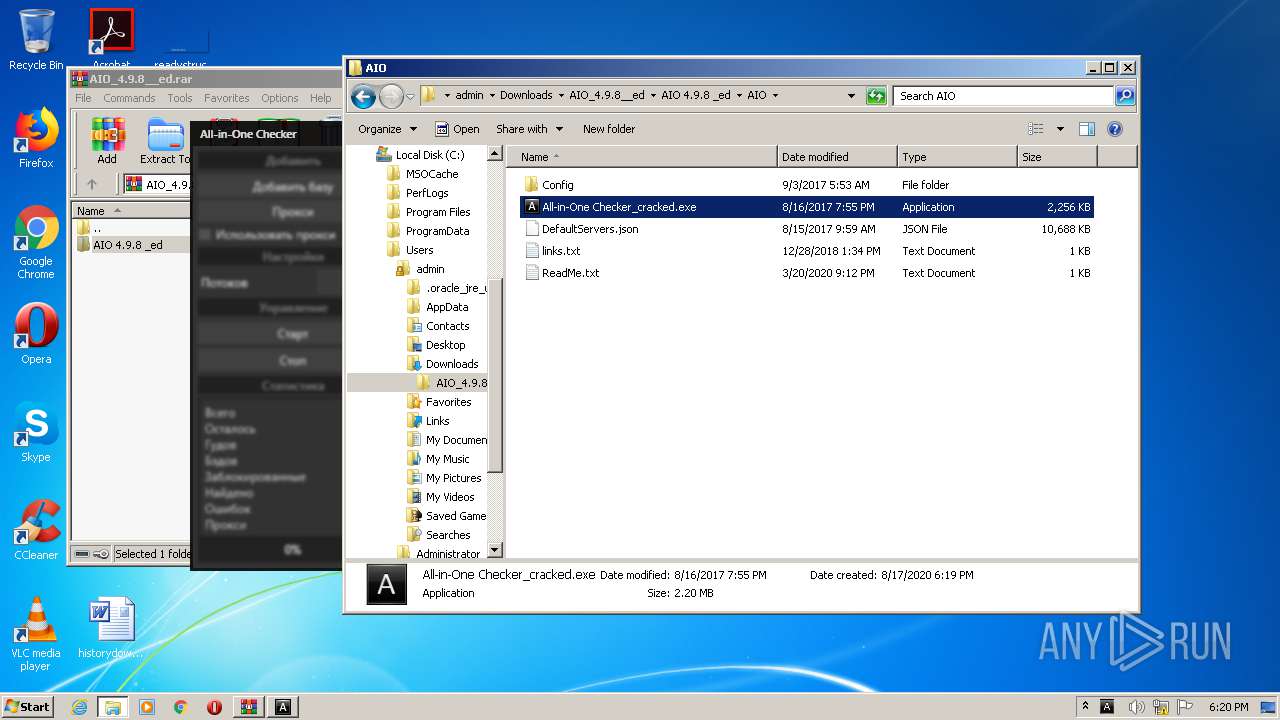
Malware analysis AIO_4.9.8__ed.rar Malicious activity

Interactive Online Malware Sandbox

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Top 10 Types of Information Security Threats for IT Teams
de
por adulto (o preço varia de acordo com o tamanho do grupo)