Malware analysis Malicious
Descrição

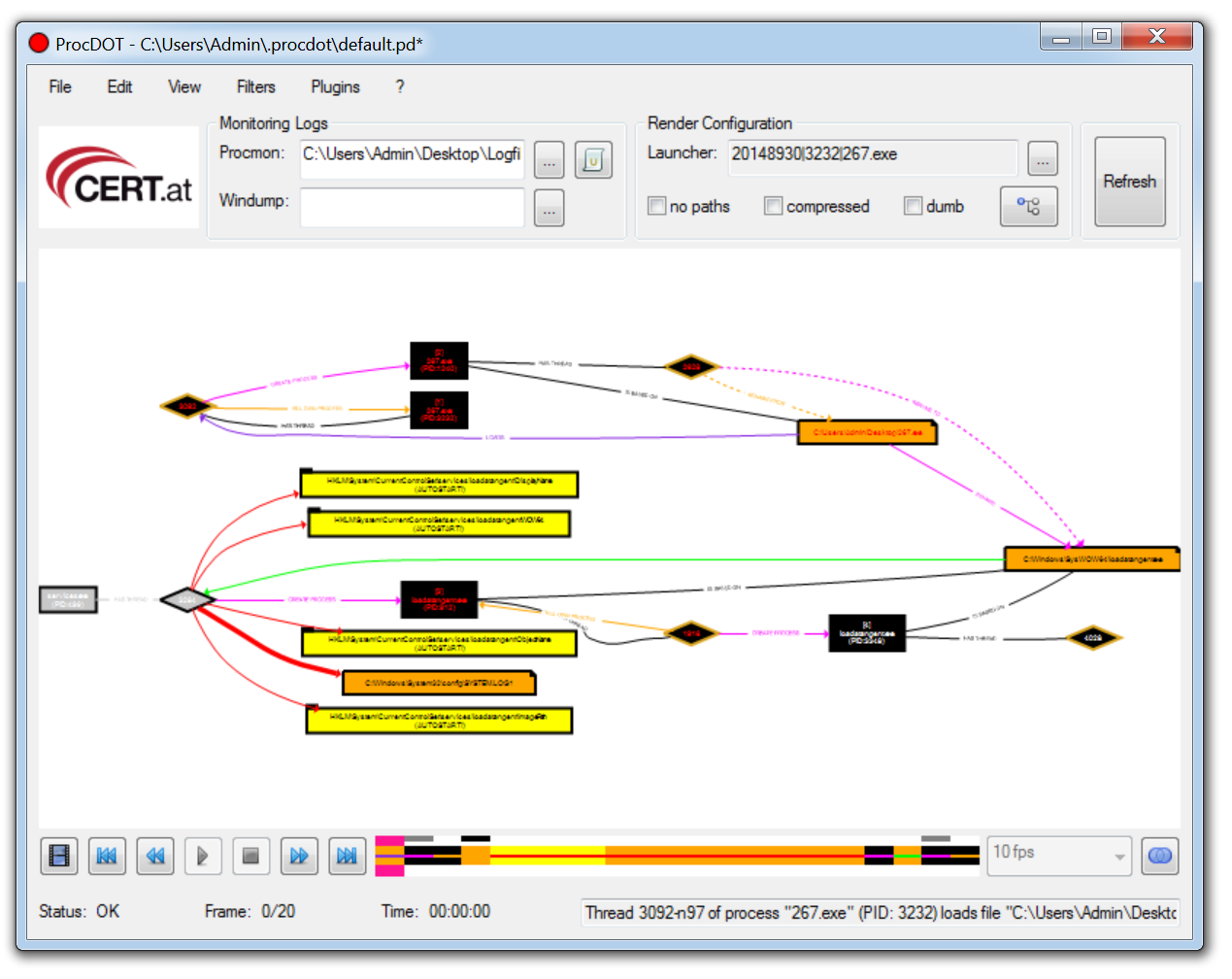
A MS word malware analysis Part2: Analyzing malicious macros
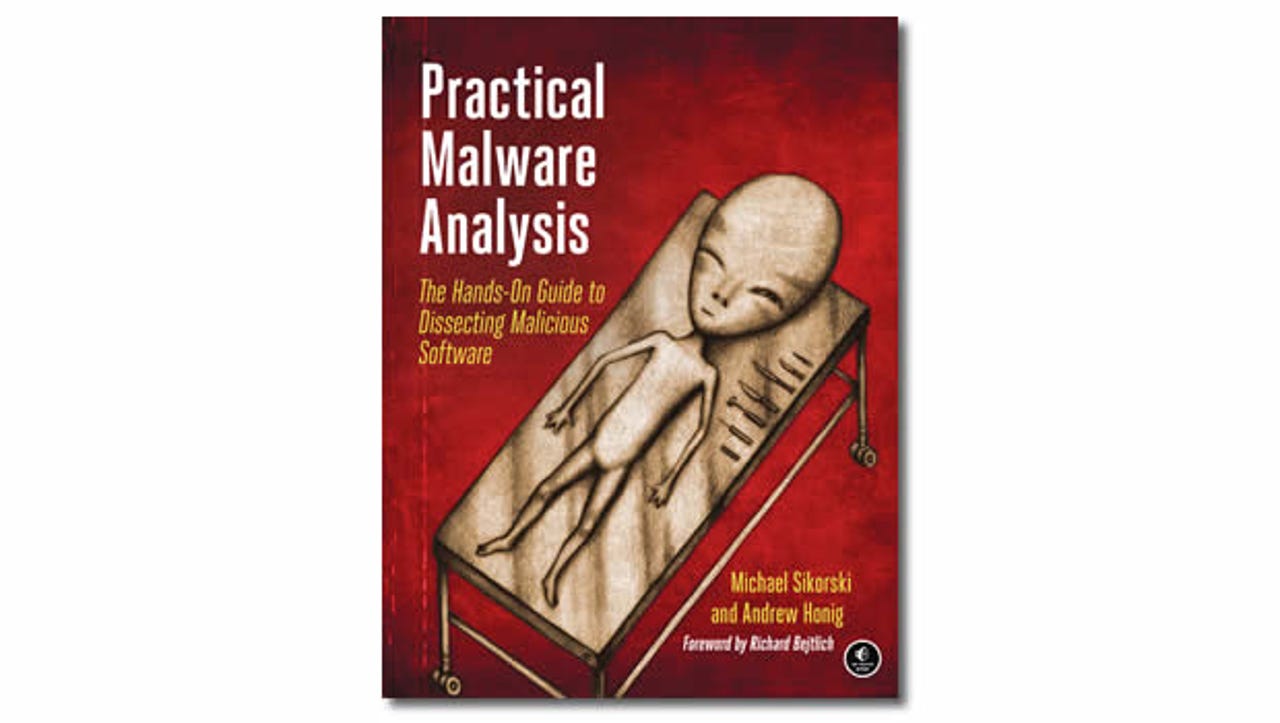
Practical Malware Analysis: Book review
What is Malware Analysis? Benefits, Types, and Tools
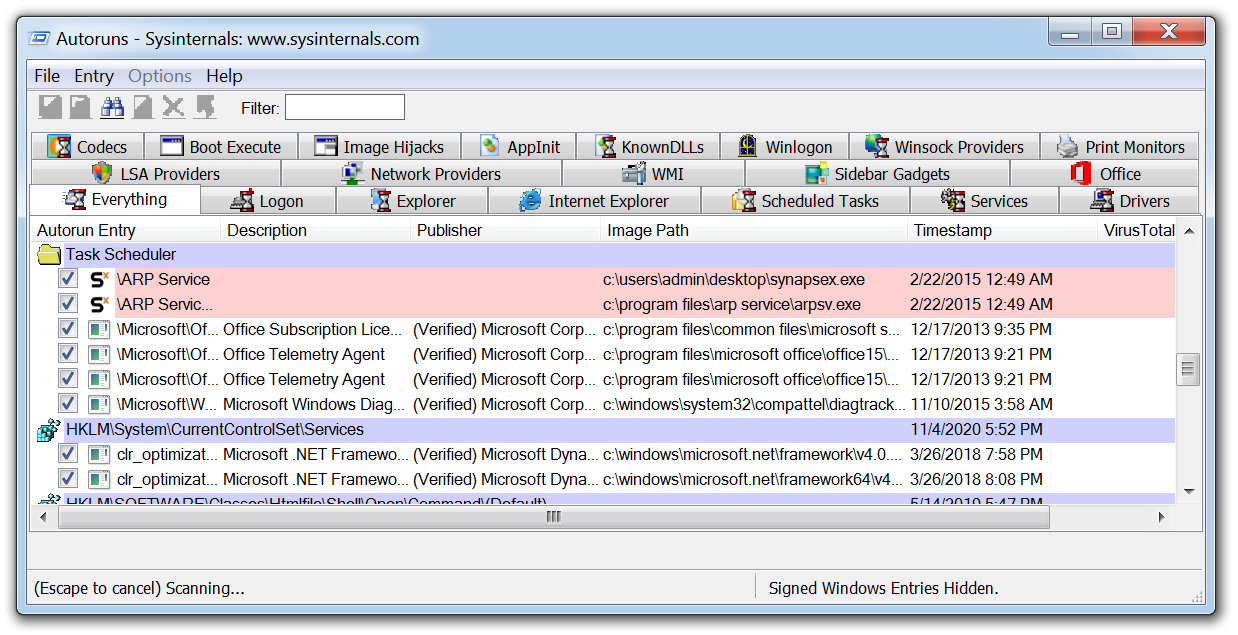
Malware Analysis 101: Handling Malicious Software Safely (Lab)
Malware Analysis Guide: Types & Tools
11 Best Malware Analysis Tools and Their Features
ChatGPT and Malware Analysis - ThreatMon - ThreatMon Blog

Malware Analysis: Steps & Examples - CrowdStrike
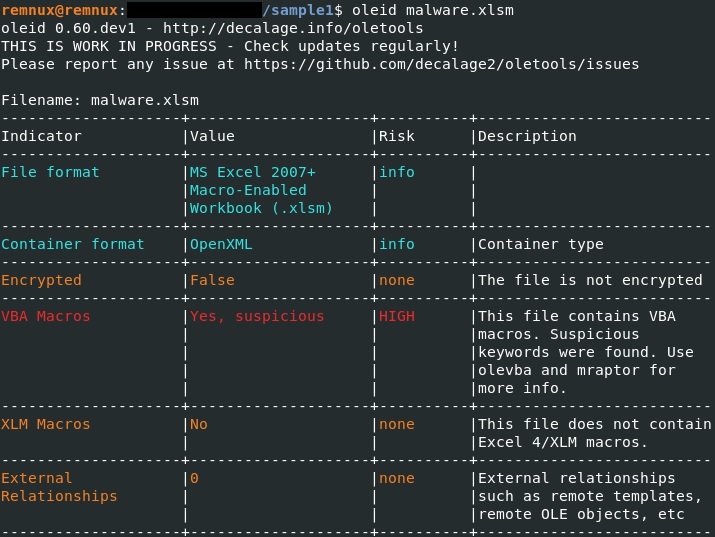
How to analyze malicious documents – Case study of an attack

Practical Malware Analysis Tutorials
REMnux Tools List for Malware Analysis
11 Best Malware Analysis Tools and Their Features
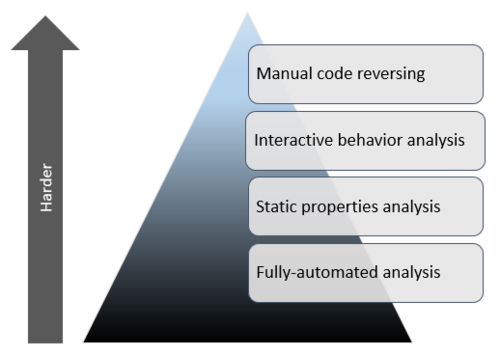
Mastering 4 Stages of Malware Analysis

Practical Malware Analysis: Book review
de
por adulto (o preço varia de acordo com o tamanho do grupo)