DigitalResidue's Forensics: Malware Incident Response pt. 2. (Collecting Volatile and Non-Volatile data)
Descrição
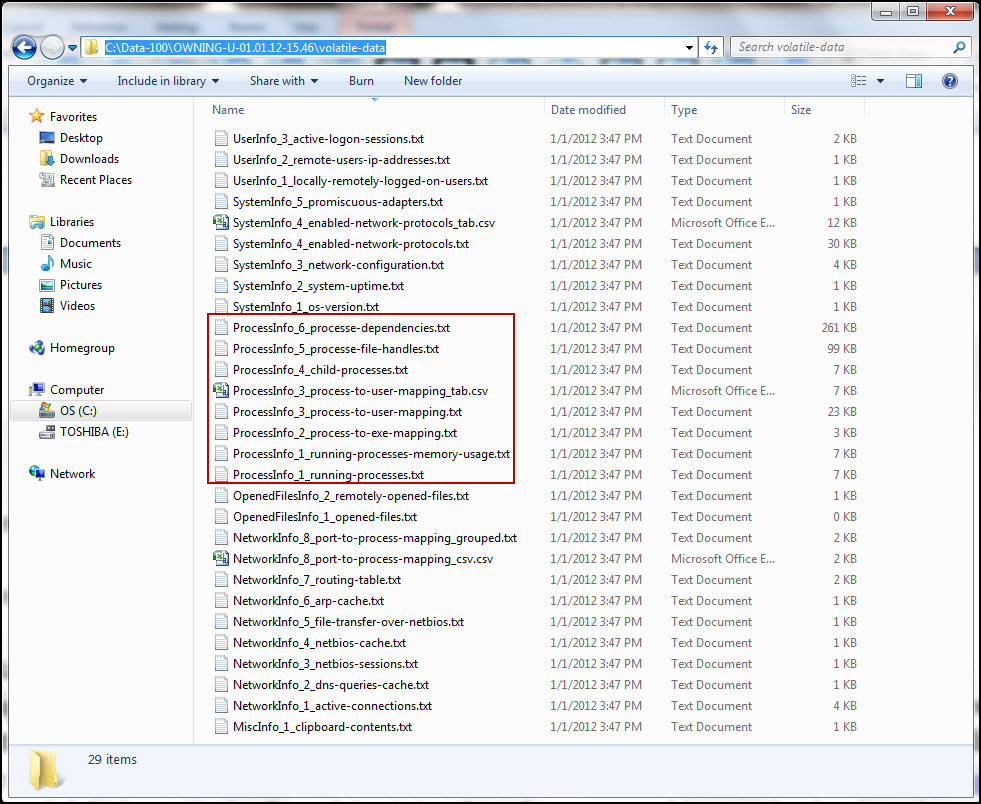
Journey Into Incident Response: Dual Purpose Volatile Data Collection Script

Incident Response: Methodology and Case Study – Fire Hunter's Blog
Memory Forensics — BlackEnergy. Hello everyone, hope everything is…, by whoami
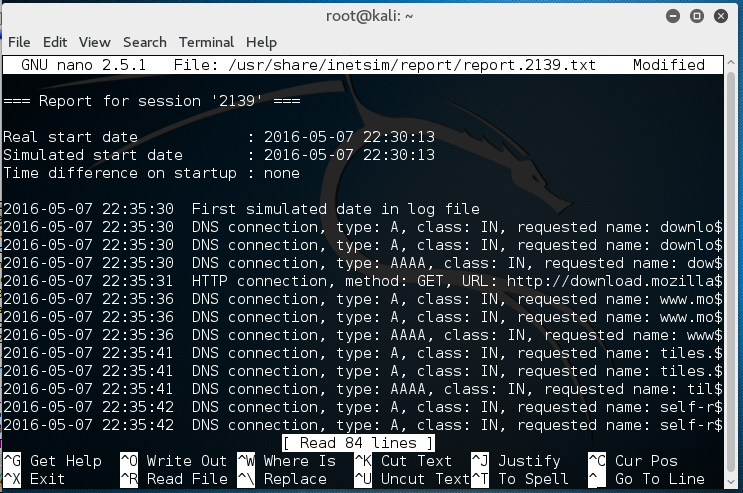
DigitalResidue's Forensics

DigitalResidue's Forensics
DigitalResidue's Forensics
CSI Evidence Indicators for Targeted Ransomware Attacks
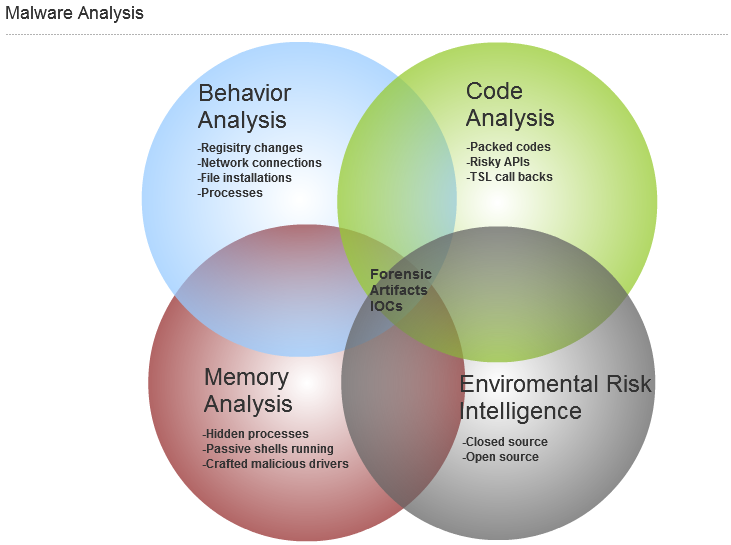
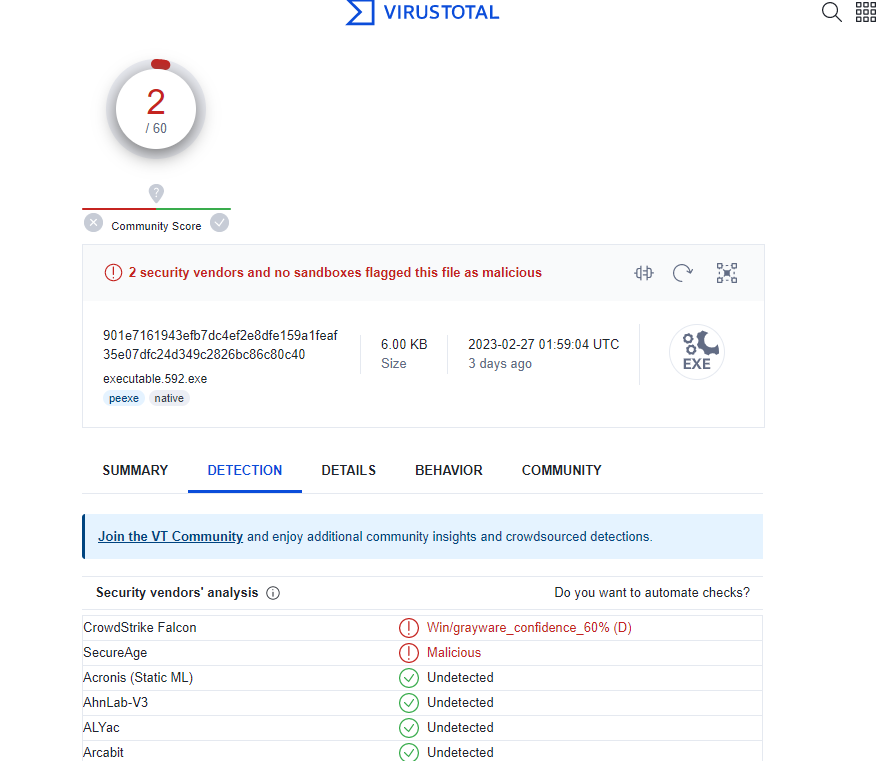
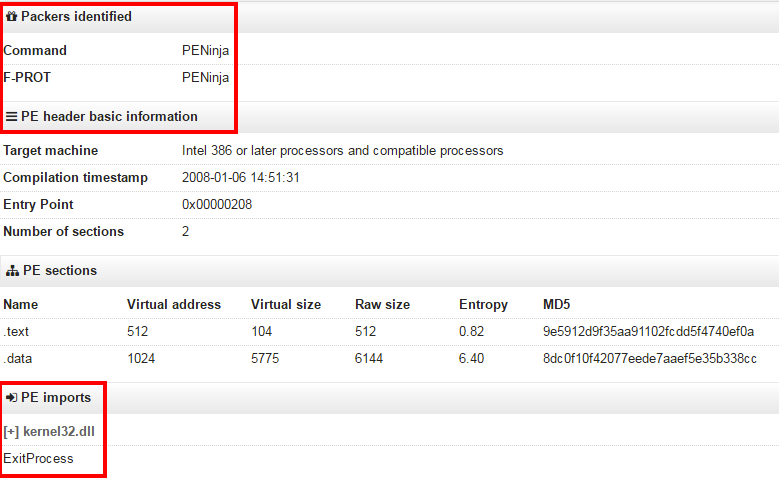
SANS Digital Forensics and Incident Response Blog, Four Focus Areas of Malware Analysis

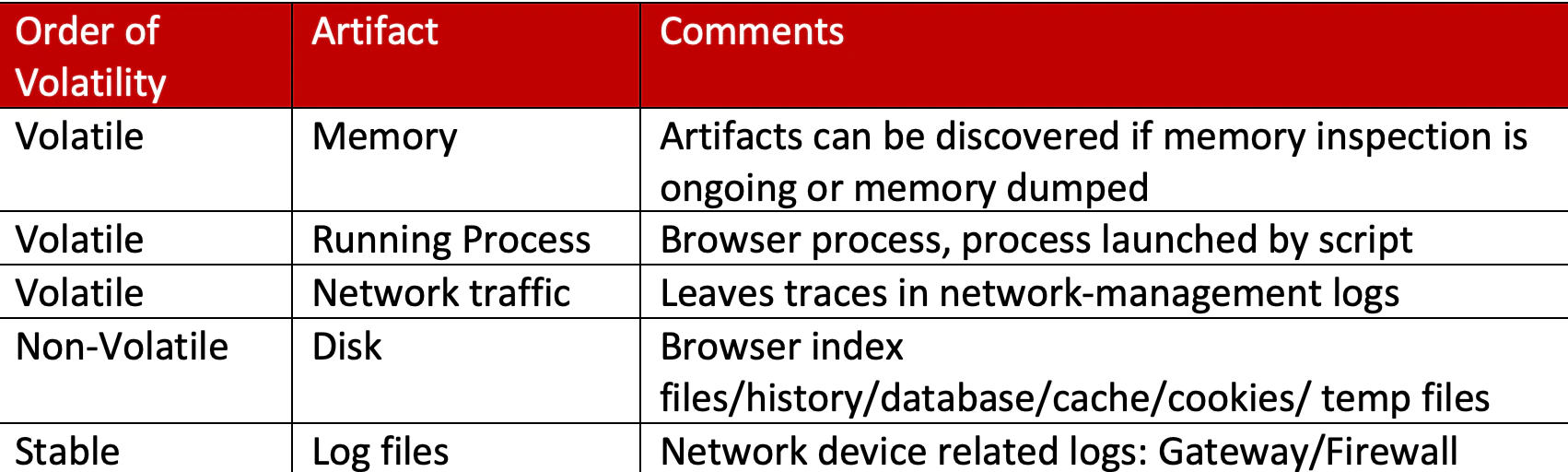
CFR and Order of Volatility - Get Certified Get Ahead

TryHackMe — DFIR: An Introduction, by exploit_daily
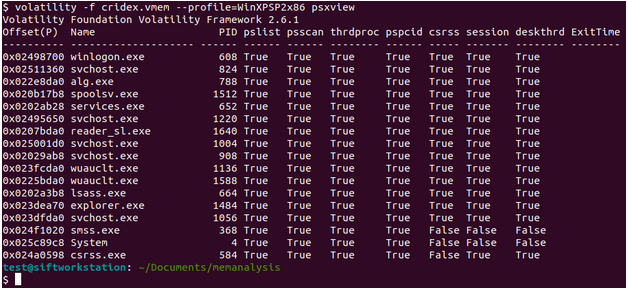
Memory CTF with Volatility Part 1 – Westoahu Cybersecurity

TryHackMe — DFIR: An Introduction, by exploit_daily
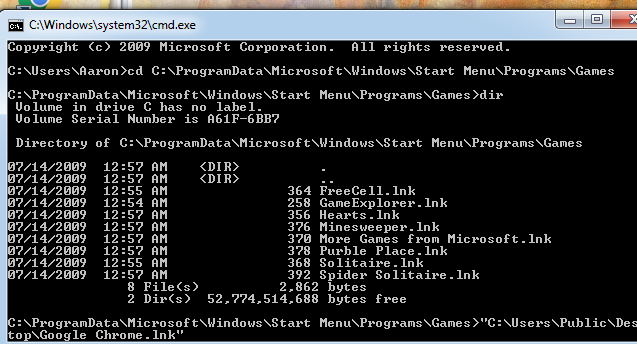
DigitalResidue's Forensics: Malware Incident Response pt. 2. (Collecting Volatile and Non-Volatile data)

DigitalResidue's Forensics
de
por adulto (o preço varia de acordo com o tamanho do grupo)