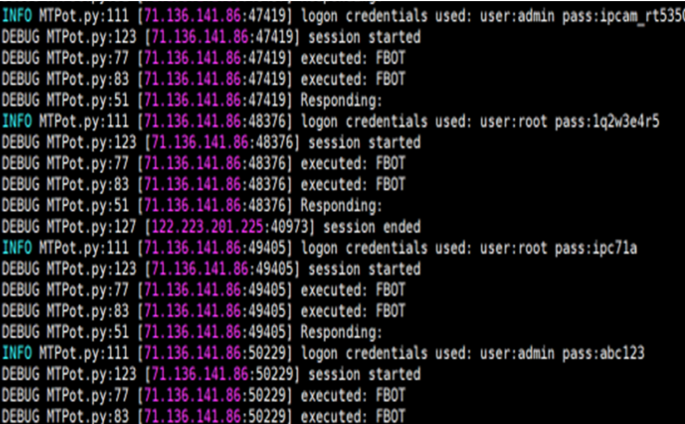
IoT Botnets: Advanced Evasion Tactics and Analysis – Part 2
Descrição
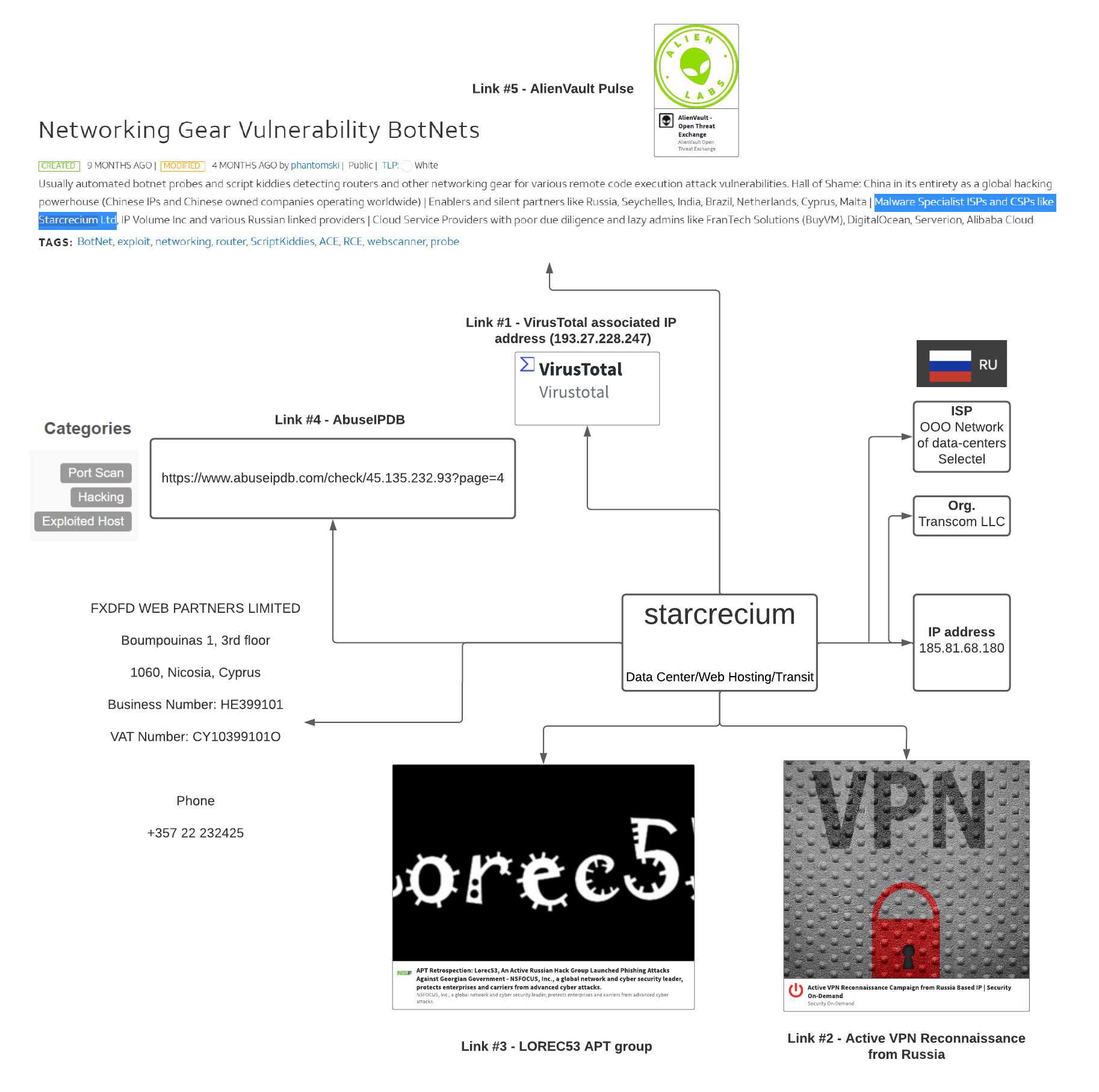
Nozomi Networks Labs analyzes new modification techniques malware authors use to evade detection and analysis tools.

PDF] A Botnets Circumspection: The Current Threat Landscape, and What We Know So Far
Detecting and confronting flash attacks from IoT botnets
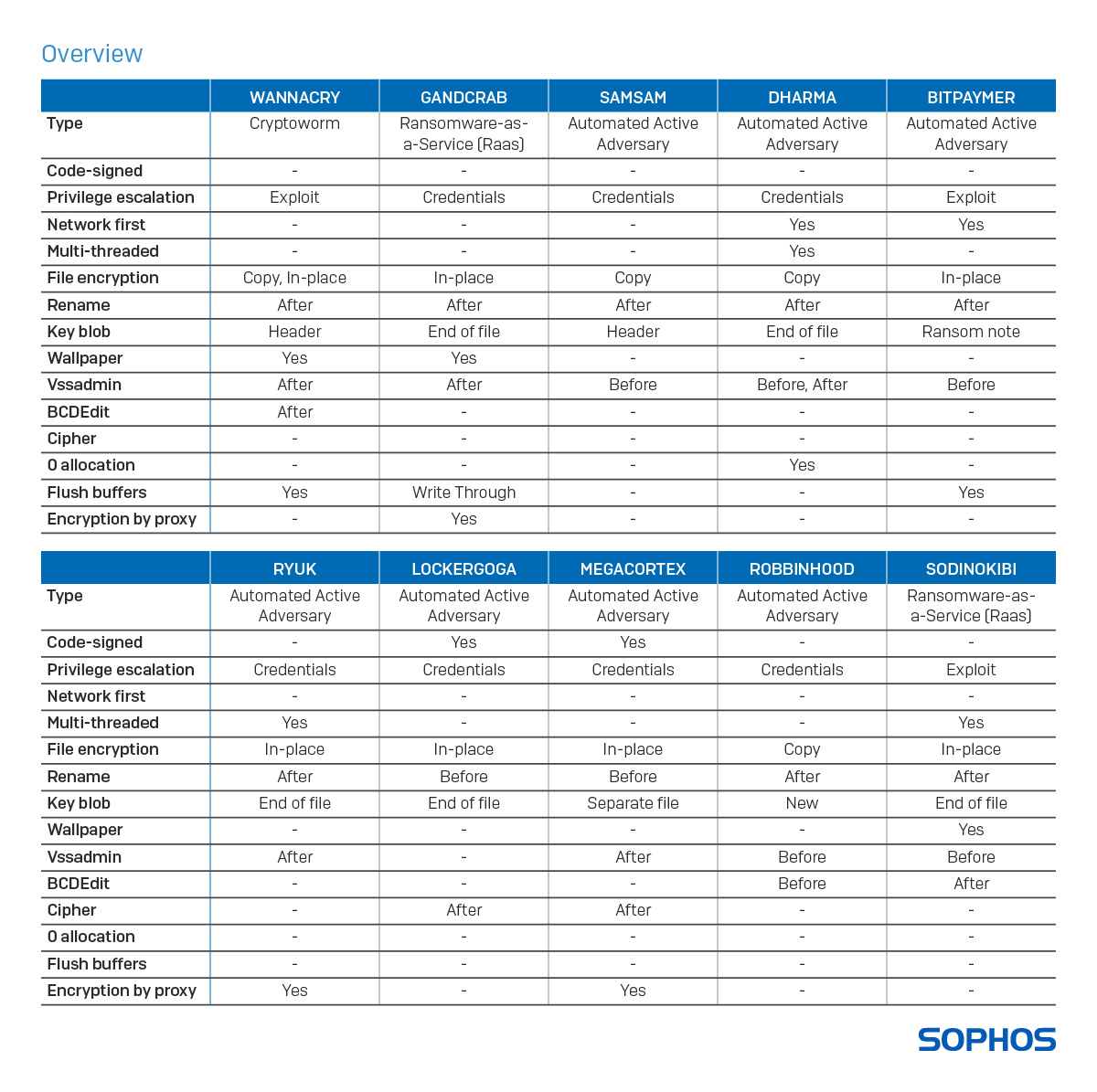
THREAT ANALYSIS REPORT: LockBit 2.0 - All Paths Lead to Ransom
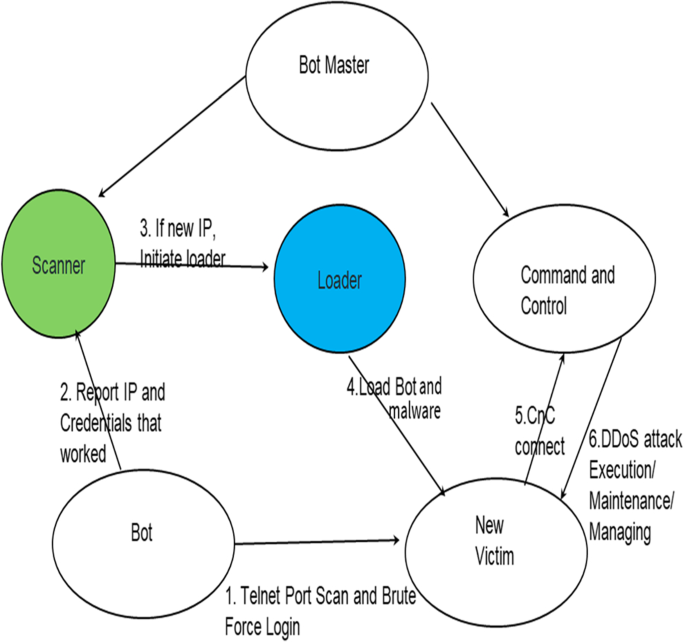
Detecting and confronting flash attacks from IoT botnets
IoT BOTNETS. IoT Botnets is abbreviated as the…, by LiveRoom
February 2020's Most Wanted Malware: Increase in Exploits Spreading the Mirai Botnet to IoT Devices - Check Point Blog

PDF] Hybrid rule-based botnet detection approach using machine learning for analysing DNS traffic

IoT Botnets: Advanced Evasion Tactics and Analysis – Part 2
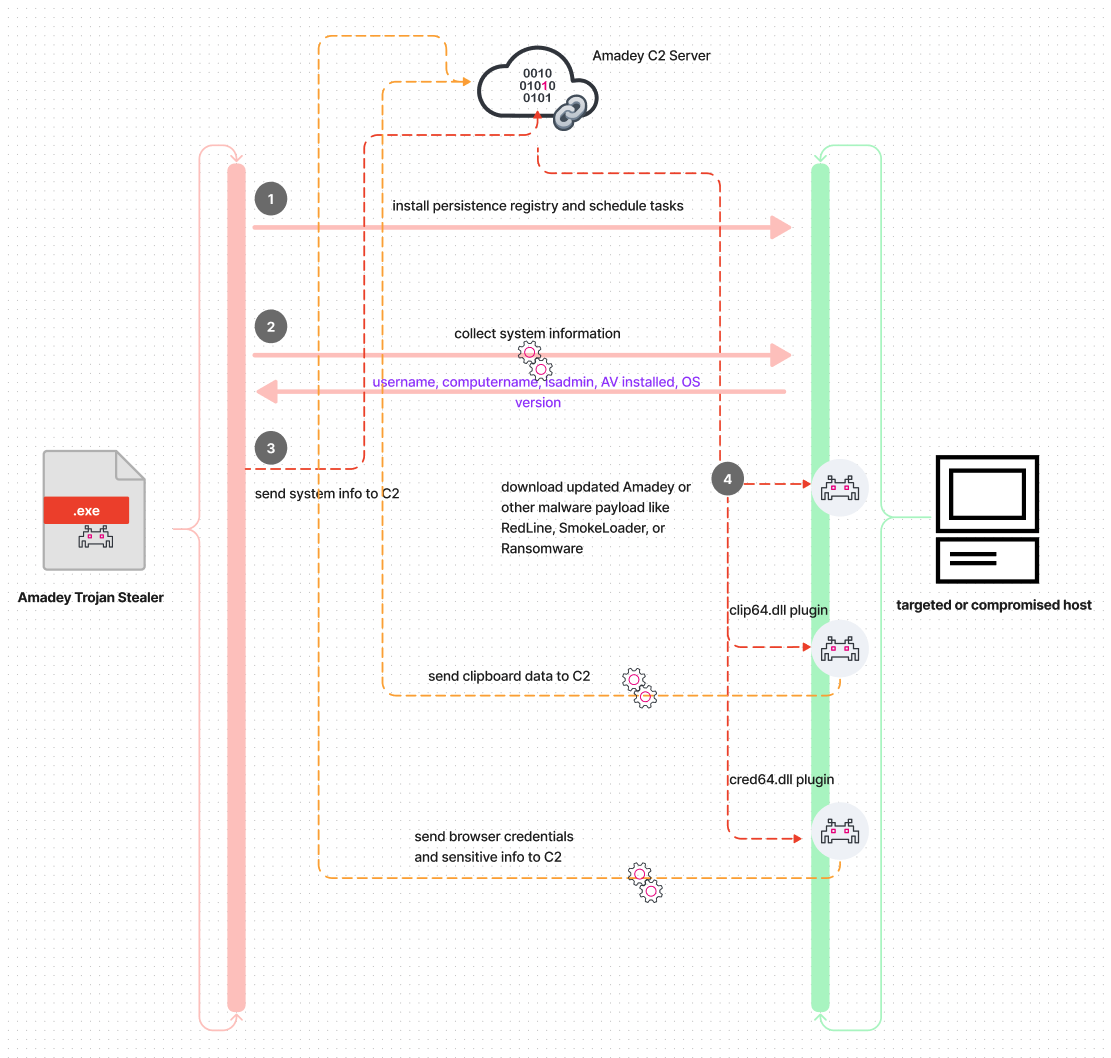
Amadey Threat Analysis and Detections

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
GitHub - dineshh912/IoT-botnet-attack-detection: Botnet detection on IoT Devices
de
por adulto (o preço varia de acordo com o tamanho do grupo)