Infrastructure Hacking: WHOIS Protocol » Hacking Lethani
Descrição
Did you know that the Secure Shell protocol, better known as SSH, is not as secure as its name suggests? In this post I show you different ways to attack this protocol. %

Hezbollah's cyber unit hacked into telecoms and ISPs

Playing with FHIR? Don't get burned, white-hat hacker cautions

7 powerful pentesting tools (& why you should stop pedestalizing them)
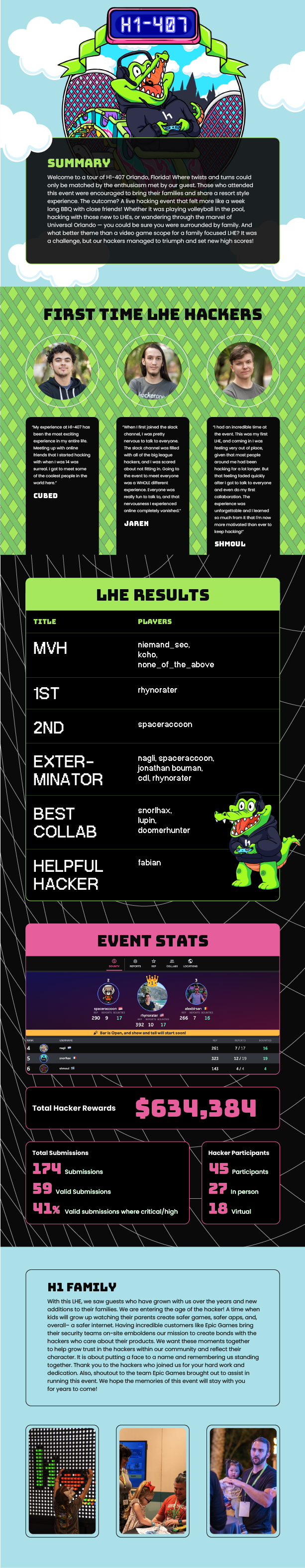
Hackers Secure Wildly Popular Video Game at H1-407
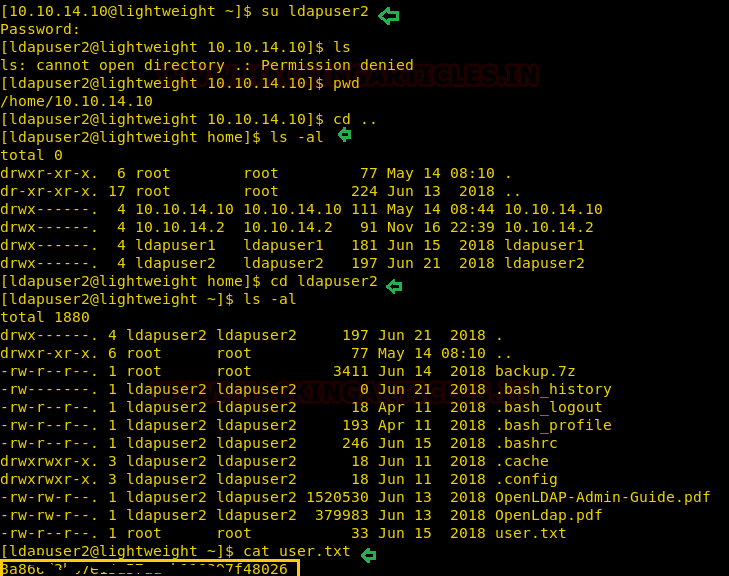
Lightweight: Hack the Box Walkthrough - Hacking Articles
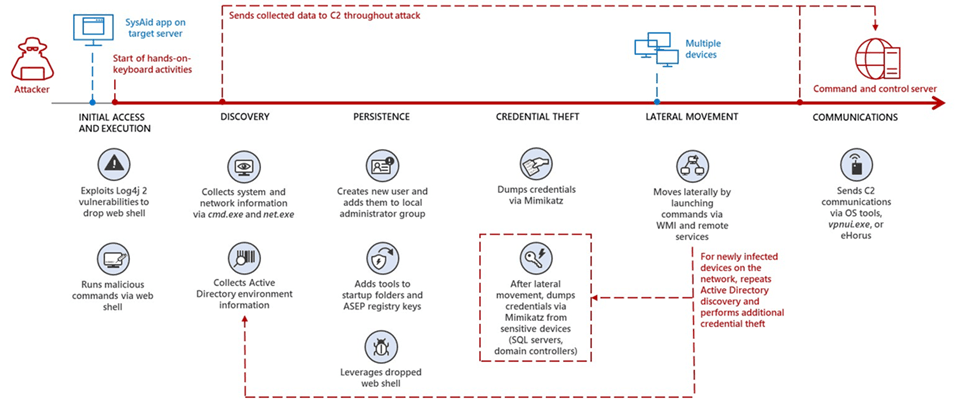
Microsoft: Nation-state Iranian hackers exploit Log4Shell against Israel

Best platforms to learn ethical hacking! - Intigriti

Infrastructure Hacking: Telnet Protocol » Hacking Lethani

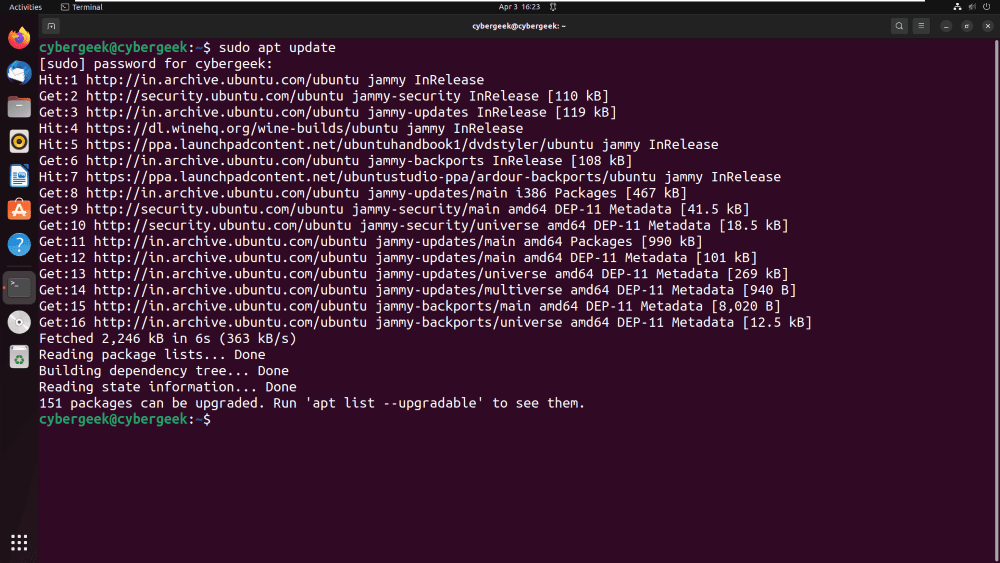
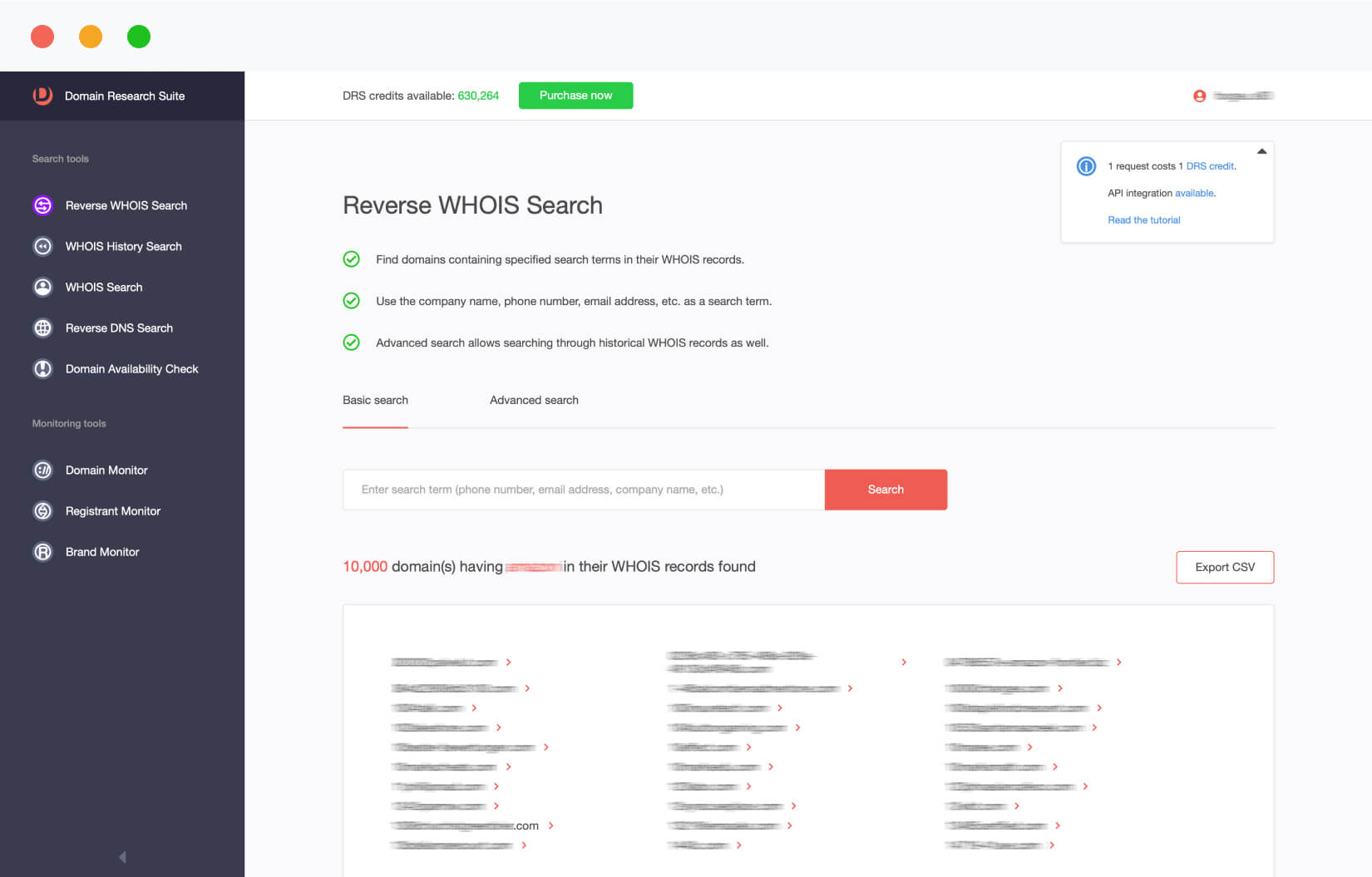
Cyber Security & Ethical Hacking - Whois ( “who owns a domain?”)

Infrastructure Hacking: WHOIS Protocol » Hacking Lethani

Hacking Tutorial - Ethical Hacking Tutorial - Wikitechy
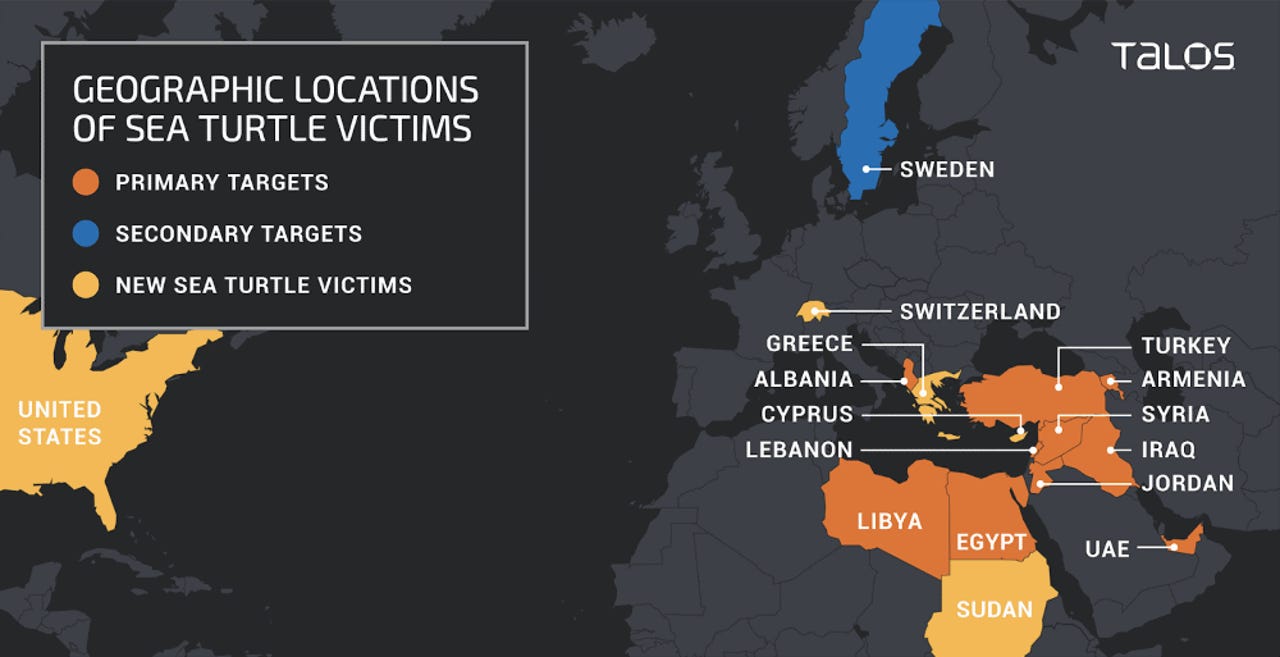
Hackers breached Greece's top-level domain registrar

Cyber Security & Ethical Hacking - Whois ( “who owns a domain?”)

tl;dr sec] #169 - Top 10 Web Hacking Techniques of 2022, Finding Malicious Dependencies, Fearless CORS
de
por adulto (o preço varia de acordo com o tamanho do grupo)