Reflected XSS Flaw: Underestimated Web Application Vulnerability
Descrição
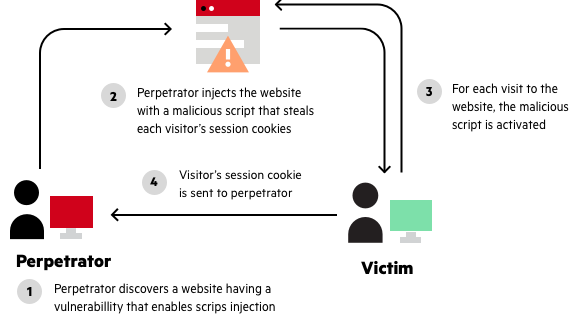
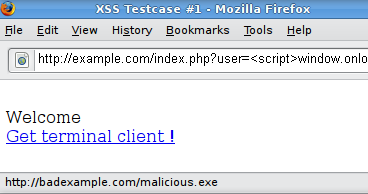
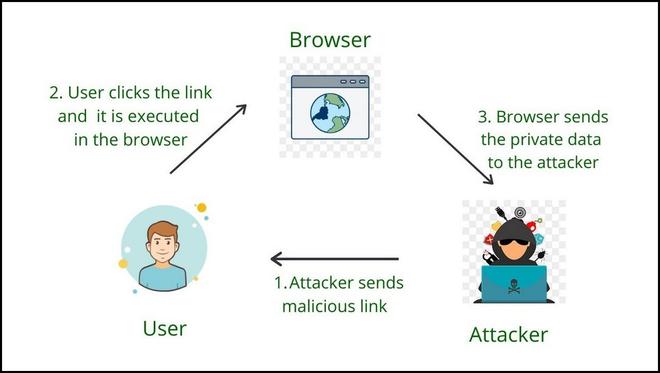
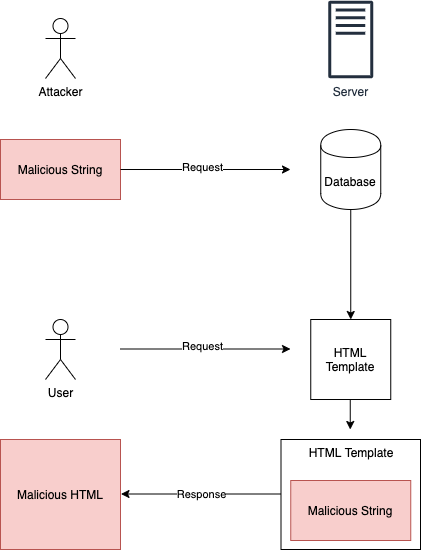
What is Reflected XSS Attack Reflected XSS attacks, also known as non-persistent attacks, occur when a malicious script is reflected off of a web application to the victim’s browser. The script is activated through a link, which sends a request to a website with a vulnerability that enables executio
Reflected XSS vulnerability for some pages in the frontend
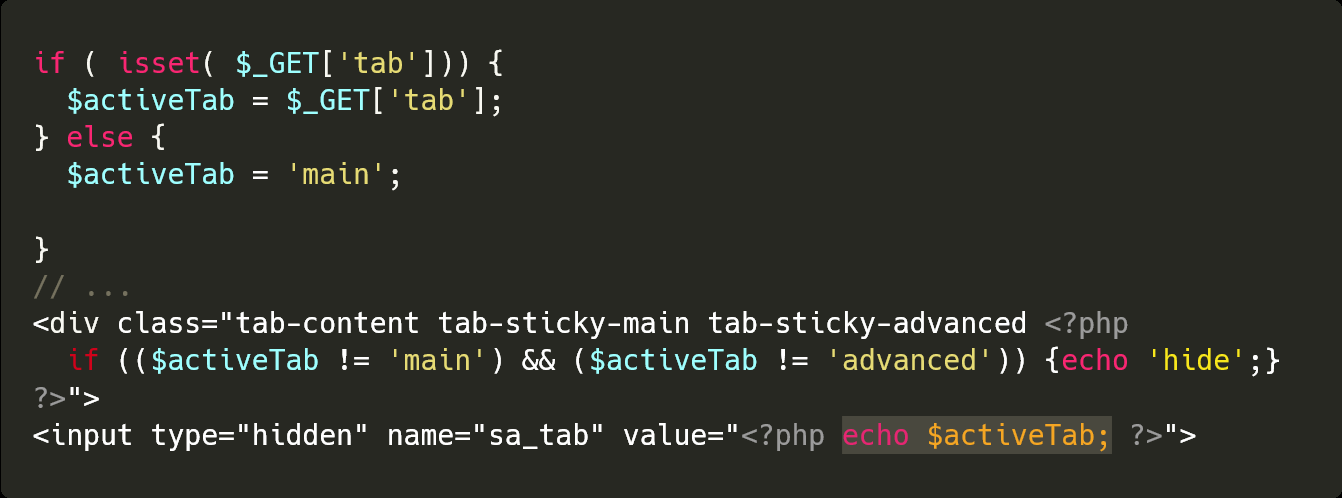
Reflected XSS in WordPress Plugin Admin Pages
Reflected XSS, How to Prevent a Non-Persistent Attack
WSTG - Latest OWASP Foundation
Reflected XSS Vulnerability in Depth - GeeksforGeeks
Cross-Site Scripting: The Real WordPress Supervillain
XSS Exploitation in Django Applications
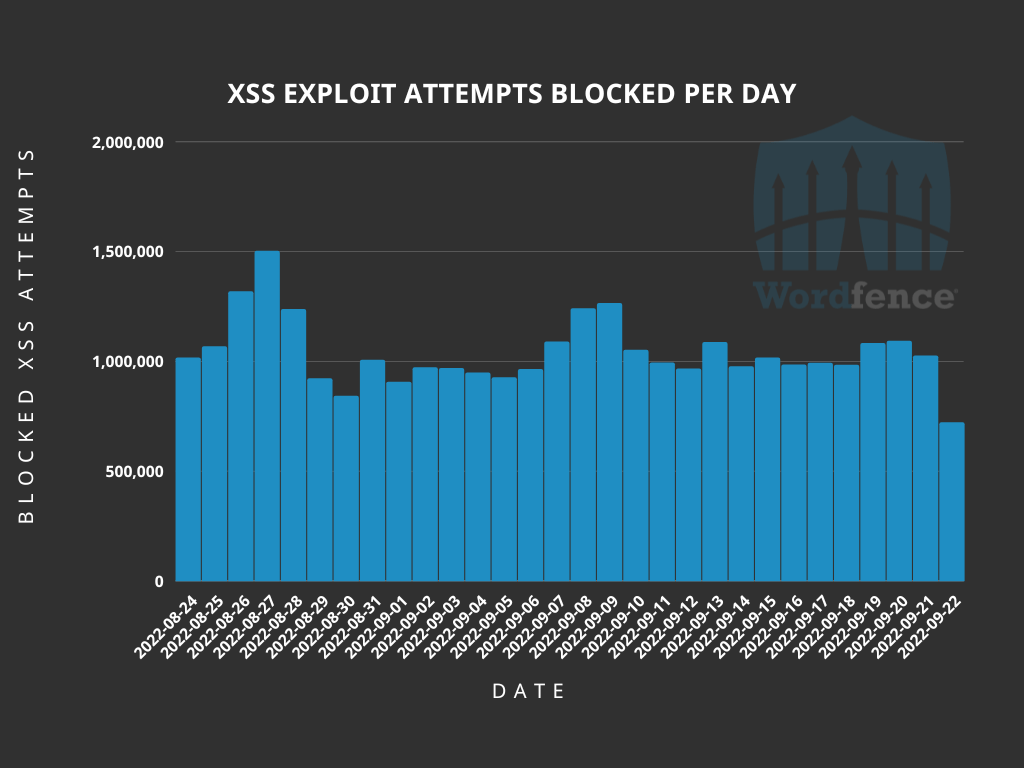
Cross-Site Scripting: The Real WordPress Supervillain

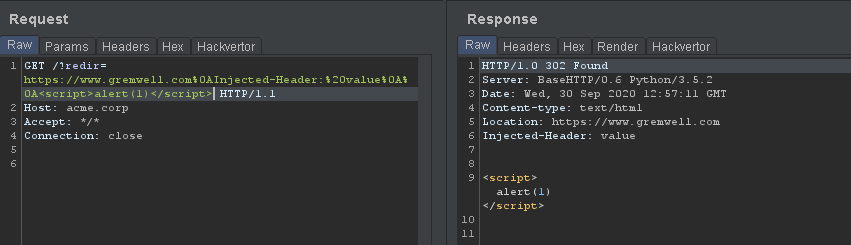
Reflected Cross-site scripting (XSS) on semrush.com redirect (bug
Cross Site-Scripting: How To Prevent An XSS Attack
Cross-Site Scripting (XSS) Course
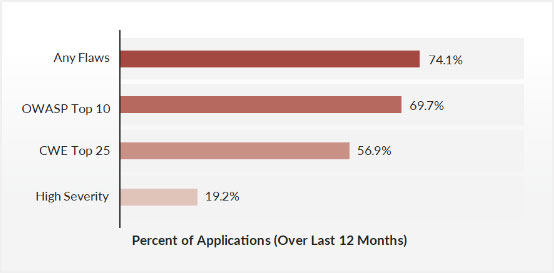
OWASP Top 10 Vulnerabilities

Reflected XSS: Examples, Testing, and Prevention

Steps to detect whether a website is vulnerable to XSS attack or

Authenticated XSS - problem or not?
de
por adulto (o preço varia de acordo com o tamanho do grupo)