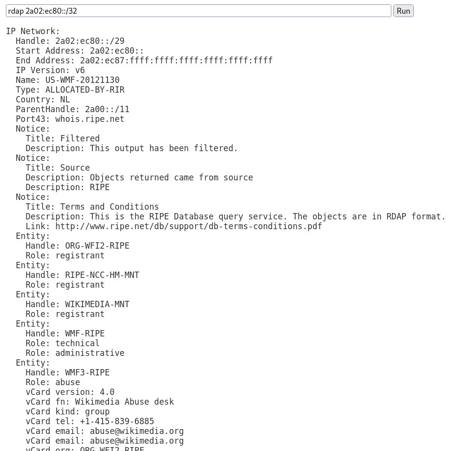
Ethical Hacking Whois Lookup - javatpoint
Descrição
Ethical Hacking | Whois Lookup with tutorial, hackers, introduction, hacking, types of hackers, famous hackers, environmental setup, network penetration testing, network hacking, etc.
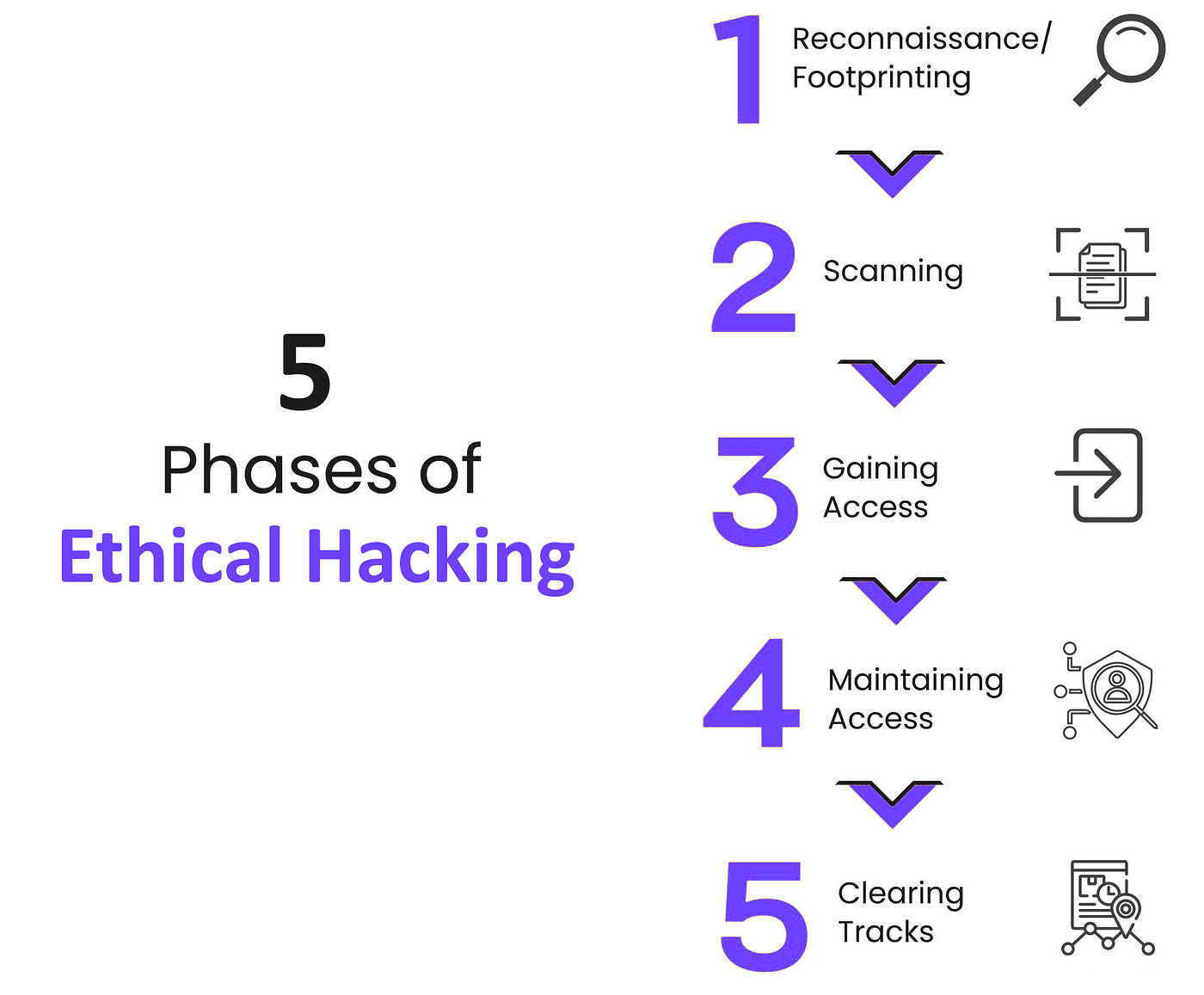
Ethical Hacking: 5 Phases, Techniques, and Tools, by Ajith Chandran

Five Phases of Ethical Hacking - ITperfection - Network Security
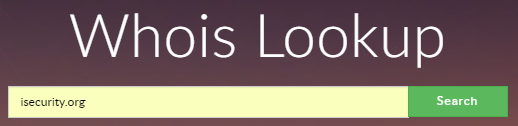
Ethical Hacking Whois Lookup - javatpoint

Ethical Hacking: What It is, Tutorial, Course, Types - javatpoint

Ethical Hacking - A SEMINAR REPORT ON “ ETHICAL HACKING ” Submitted To SAVITRIBAI PHULE PUNE - Studocu
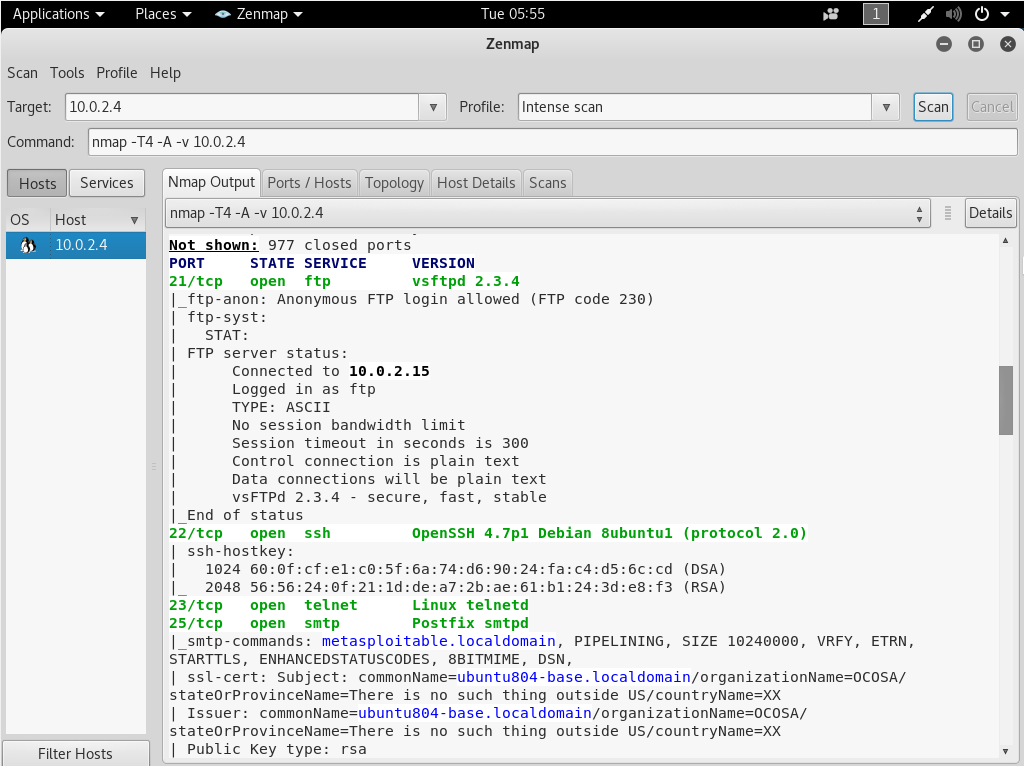
Ethical Hacking Server-side Attack Basics - javatpoint
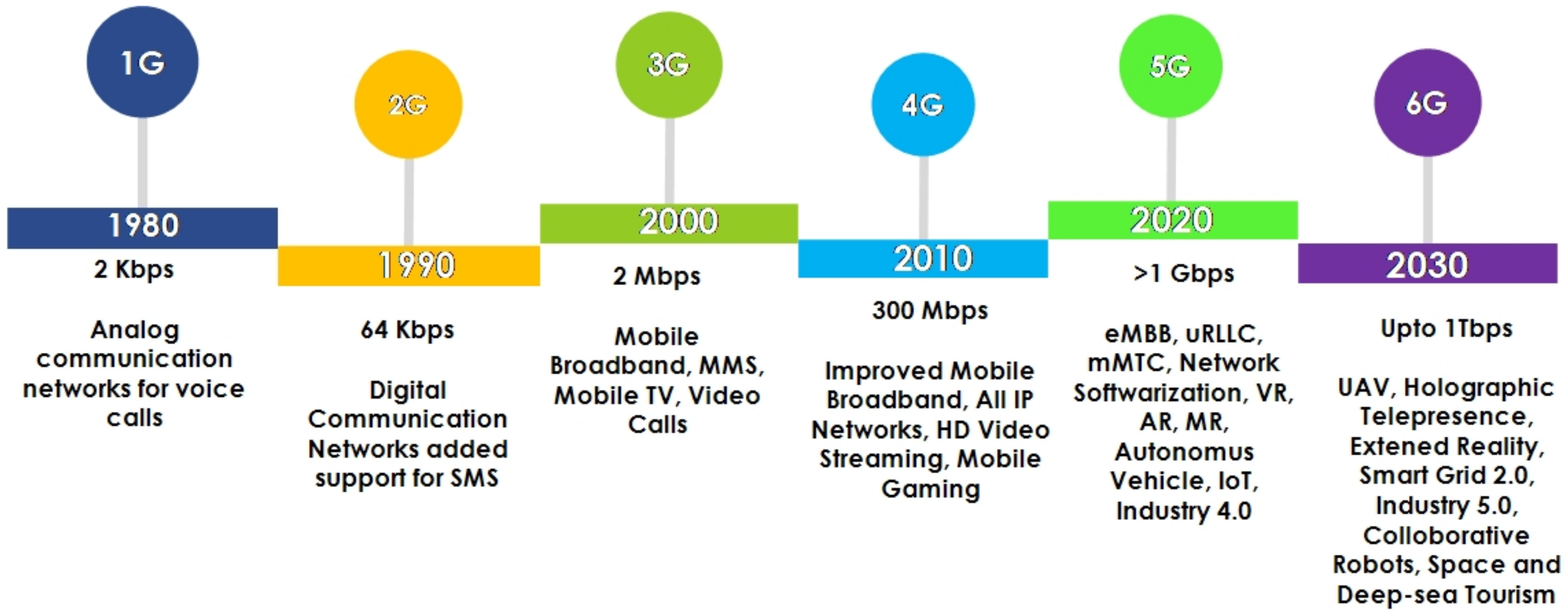
Sensors, Free Full-Text

How to Become an Ethical Hacker in 2023?
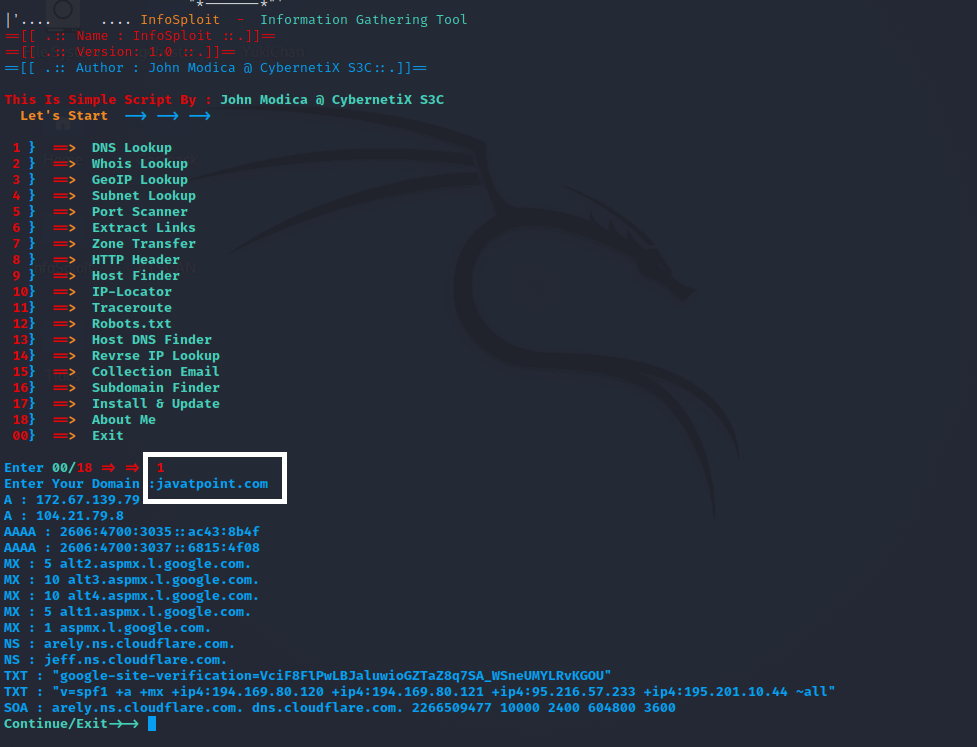
InfoSploit-Information Gathering Tool in Kali Linux - javatpoint
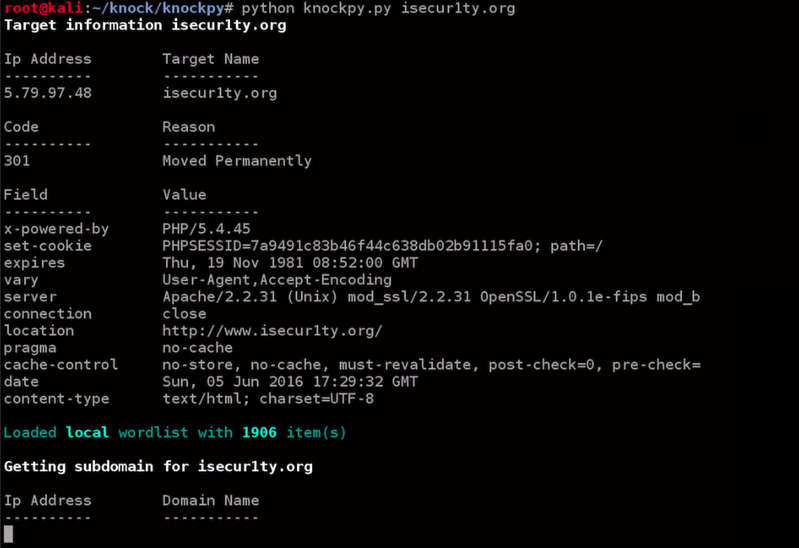
Ethical Hacking Discovering Subdomain - javatpoint
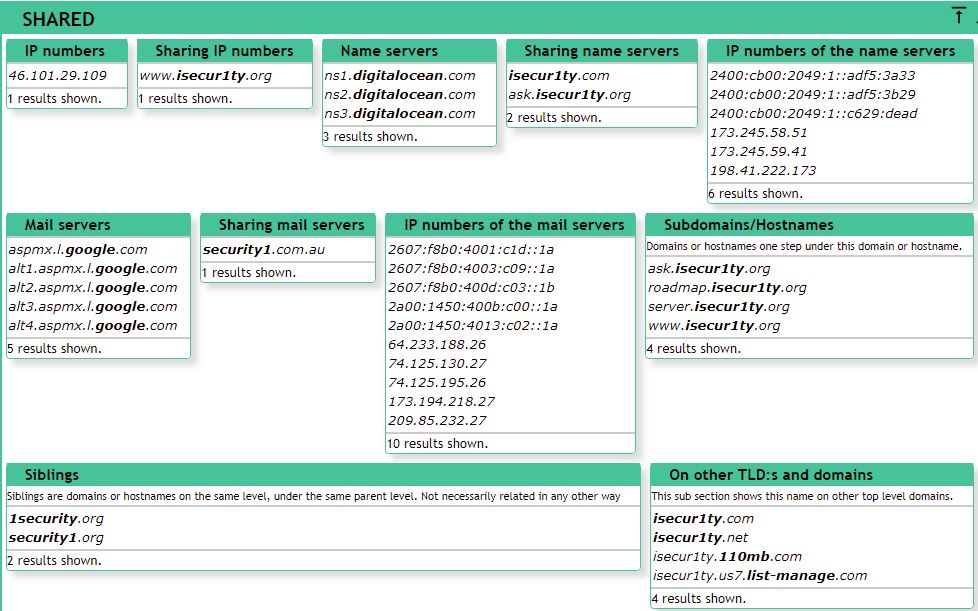
Ethical Hacking Robtex - javatpoint
de
por adulto (o preço varia de acordo com o tamanho do grupo)