Detecting Linux Anti-Forensics: Timestomping
Descrição
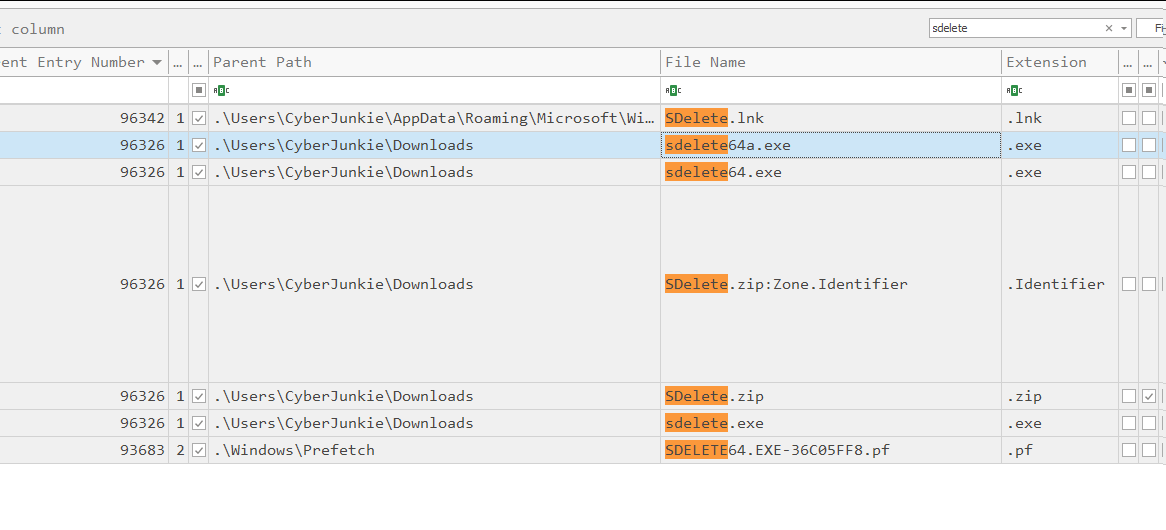
#160; Threat actors can modify the timestamps on malicious files to evade detection. This technique has been used time and time again across va
5 anti-forensics techniques to trick investigators (+ examples

Windows MACB Timestamps (NTFS Forensics)
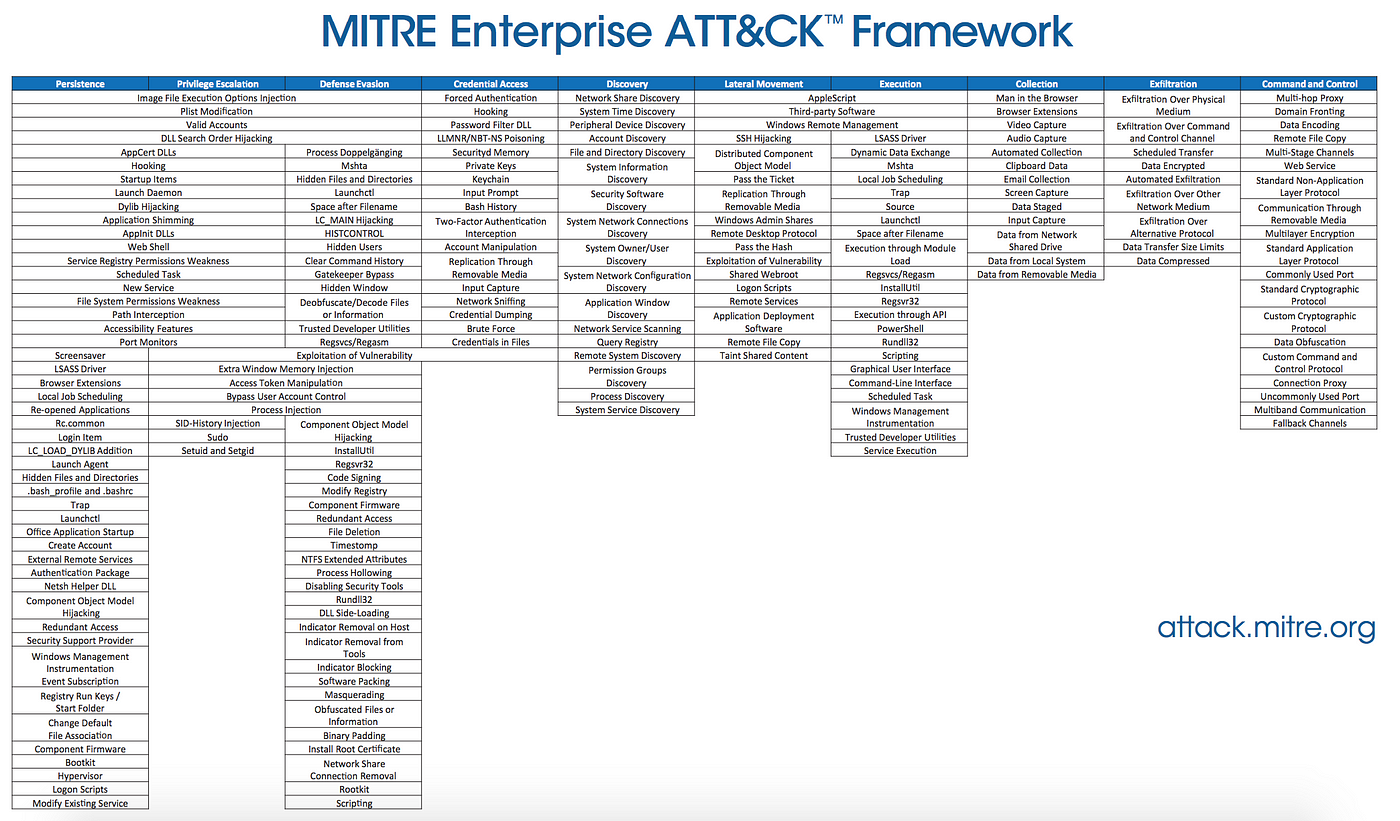
Forensic detection of MITRE ATT&CK Techniques
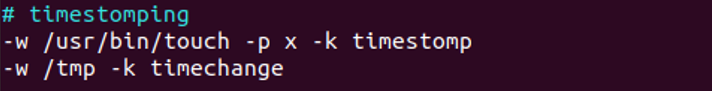
Detecting Linux Anti-Forensics: Timestomping

Detecting Linux Anti-Forensics Log Tampering
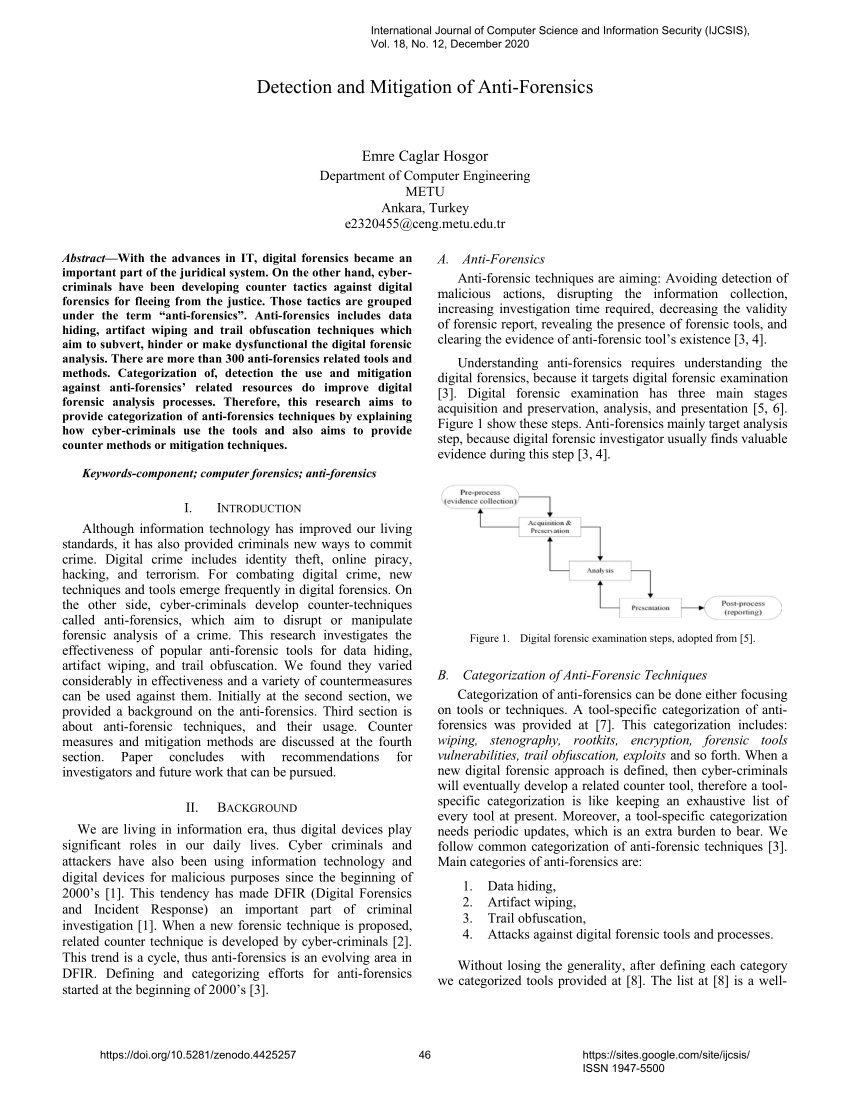
PDF) Detection and Mitigation of Anti-Forensics

Lina L. en LinkedIn: Detecting Linux Anti-Forensics: Timestomping

Lina L. en LinkedIn: Detecting Linux Anti-Forensics: Timestomping
Anti-Forensic Techniques Used By Lazarus Group - ASEC BLOG

Anti-Forensic Techniques - HackTricks
de
por adulto (o preço varia de acordo com o tamanho do grupo)




/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2022/m/7/KDbZ9pSiAvniRTLYp2oA/to1alwyyji6f1650416308086.png)
