Algorithms, Free Full-Text
Descrição
Authentication protocols are expanding their application scope in wireless information systems, among which are low-orbit satellite communication systems (LOSCS) for the OneWeb space Internet, automatic object identification systems using RFID, the Internet of Things, intelligent transportation systems (ITS), Vehicular Ad Hoc Network (VANET). This is due to the fact that authentication protocols effectively resist a number of attacks on wireless data transmission channels in these systems. The main disadvantage of most authentication protocols is the use of symmetric and asymmetric encryption systems to ensure high cryptographic strength. As a result, there is a problem in delivering keys to the sides of the prover and the verifier. At the same time, compromising of keys will lead to a decrease in the level of protection of the transmitted data. Zero-knowledge authentication protocols (ZKAP) are able to eliminate this disadvantage. However, most of these protocols use multiple rounds to authenticate the prover. Therefore, ZKAP, which has minimal time costs, is developed in the article. A scheme for adapting protocol parameters has been developed in this protocol to increase its efficiency. Reductions in the level of confidentiality allow us to reduce the time spent on the execution of the authentication protocol. This increases the volume of information traffic. At the same time, an increase in the confidentiality of the protocol entails an increase in the time needed for authentication of the prover, which reduces the volume of information traffic. The FPGA Artix-7 xc7a12ticsg325-1L was used to estimate the time spent implementing the adaptive ZKAP protocol. Testing was performed for 32- and 64-bit adaptive authentication protocols.

Machine Learning Algorithms - Second Edition
Algorithms, Free Full-Text
Genetic Algorithms And Investment Strategies Download - Colaboratory

What is A* Search Algorithm? A* (star) Algorithm in AI 2024

PDF) Comparison of quantification algorithms for circulating cell

Search algorithm - Wikipedia

ACLS algorithm overview
Stochastic Gradient Descent Algorithm With Python and NumPy – Real
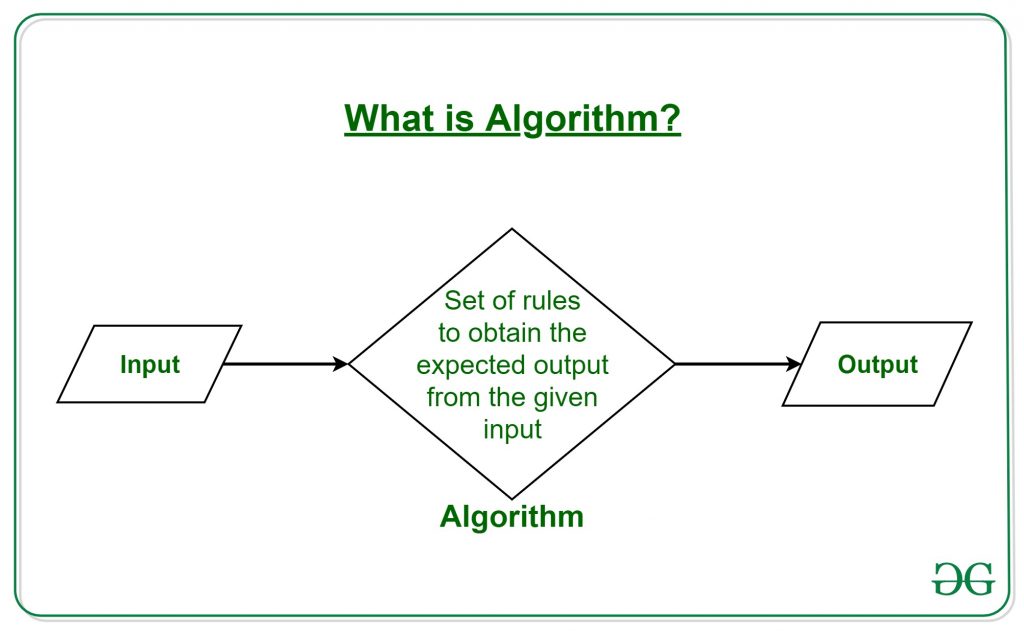
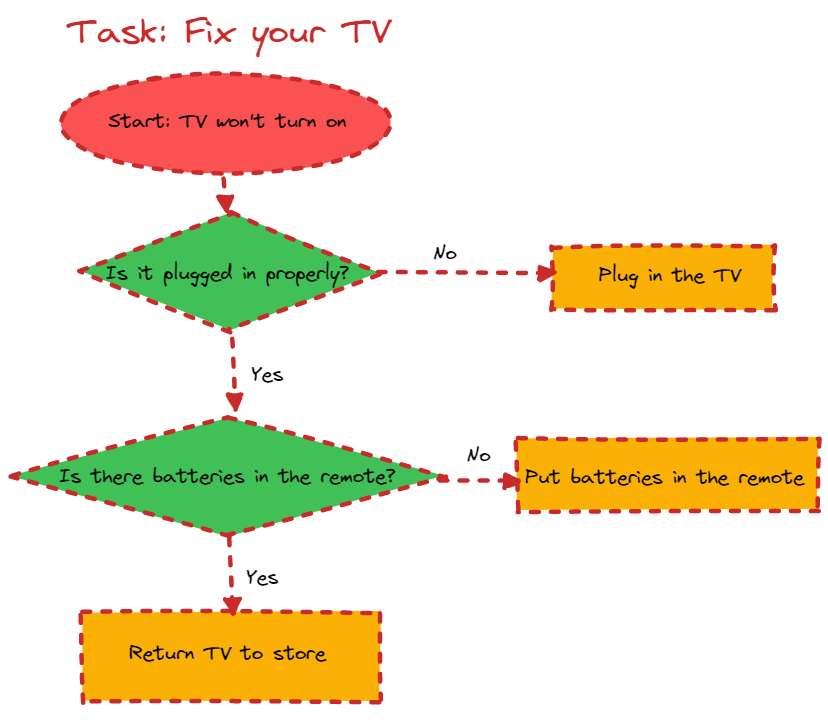
What is Algorithm Introduction to Algorithms - GeeksforGeeks

Screening for extranodal extension in HPV-associated oropharyngeal
The Algorithms Illuminated Book Series

Free Download Algorithms of Oppression: How Search Engines

Comparative analysis of the BVTNet with baseline algorithms for

Industrial Algorithms
AlgoDaily - Algorithm Examples In Everyday Life
de
por adulto (o preço varia de acordo com o tamanho do grupo)







